Surge of MegaCortex ransomware attacks detected

UK cyber-security firm Sophos reported detecting a spike in ransomware attacks at the end of last week from a new strain named MegaCortex.
Sophos said the ransomware appears to have been designed to target large enterprise networks as part of carefully planned targeted intrusions --in a tactic that is known as "big-game hunting."
The modus operandi is not new and has been the preferred method of delivering ransomware for almost half a year.
MegaCortex now joins an ever-growing list of ransomware strains that cyber-criminal groups are using only in targeted attacks, rather than with spam or other mass deployment techniques. The list includes some recognizable names, such as Ryuk, Bitpaymer, Dharma, SamSam, LockerGoga, and Matrix.
Sudden rise of attacks this month
According to a report Sophos released late Friday night last week, MegaCortex was first spotted back in late January, when someone uploaded a sample on malware scanning service VirusTotal.
Since then, the number of attacks has been growing, but they spiked mid last week when Sophos says it detected 47 attacks --accounting for two-thirds of all the 76 MegaCortex attacks the company has seen all year.
Sophos says it blocked the attacks it detected, which originated from enterprise networks located in the United States, Canada, the Netherlands, Ireland, Italy, and France. However, other attacks might have occurred in other places where the UK antivirus vendor had no coverage.
Rietspoof infection vector?
While Sophos was not able to pinpoint with certainty how MegaCortex got on infected hosts, several cyber-security researchers tweeted over the weekend that the ransomware appears to be dropped on attacked networks via a malware loader named Rietspoof.
We also decided to create a simple #YARA rule to detect #rietspoof loader used with #megacortex https://t.co/la1527yJiH @McAfee_Labs
— Marc Rivero López (@Seifreed) May 6, 2019
Yes, indeed. So this appears to be #Rietspoof loader found part of the #MegaCortex installation hmm. That is an interesting twist, indeed as this loader looked very familiar to me 😉. @malwrhunterteam found it first here -> https://t.co/xvXnyD5mco
— Vitali Kremez (@VK_Intel) May 4, 2019
This is a new approach compared to past "targeted ransomware attacks" that either relied on:
- hacker groups brute-forcing weakly-secured RDP endpoints;
- dropping ransomware as a second-stage payload on workstations previously infected with the Emotet or Trickbot trojans.
But despite the delivery method, MegaCortex appears to be just as dangerous as the other "big-game hunting" ransomware strains, with hackers quickly escalating their access to a domain controller, from where they try to deploy the ransomware to as many internal workstations as possible.
Since this appears to be a common practice for most ransomware families that are being used in targeted attacks, Sophos researchers recommend that companies adopt two-factor authentication for internal networks, and especially for central management servers.
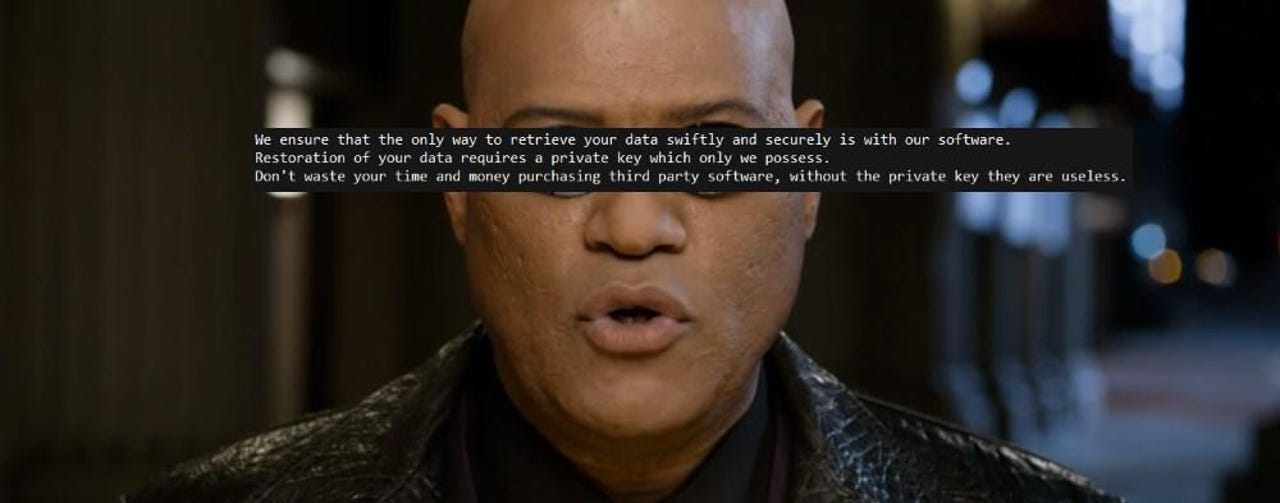
Victims can recognize the ransomware by the random eight-character extension it adds to encrypted files, but also its ransom note, which is embedded below.
Slack tips and tricks: Master the art of workplace collaboration
Related malware and cybercrime coverage:
- A hacker is wiping Git repositories and asking for a ransom
- Hackers steal card data from 201 online campus stores from Canada and the US
- Windows Server hosting provider still down a week after ransomware attack
- Mysterious hacker has been selling Windows 0-days to APT groups for three years
- Malvertiser behind 100+ million bad ads arrested and extradited to the US
- Hacker takes over 29 IoT botnets
- Hackers impersonate Microsoft more than any other brand in phishing attacks TechRepublic
- Game of Thrones has the most malware of any pirated TV show CNET