Windows Server hosting provider still down a week after ransomware attack

A ransomware infection has crippled the operations of a US-based web hosting provider for almost eight days now, several of the company's disgruntled customers have told ZDNet today.
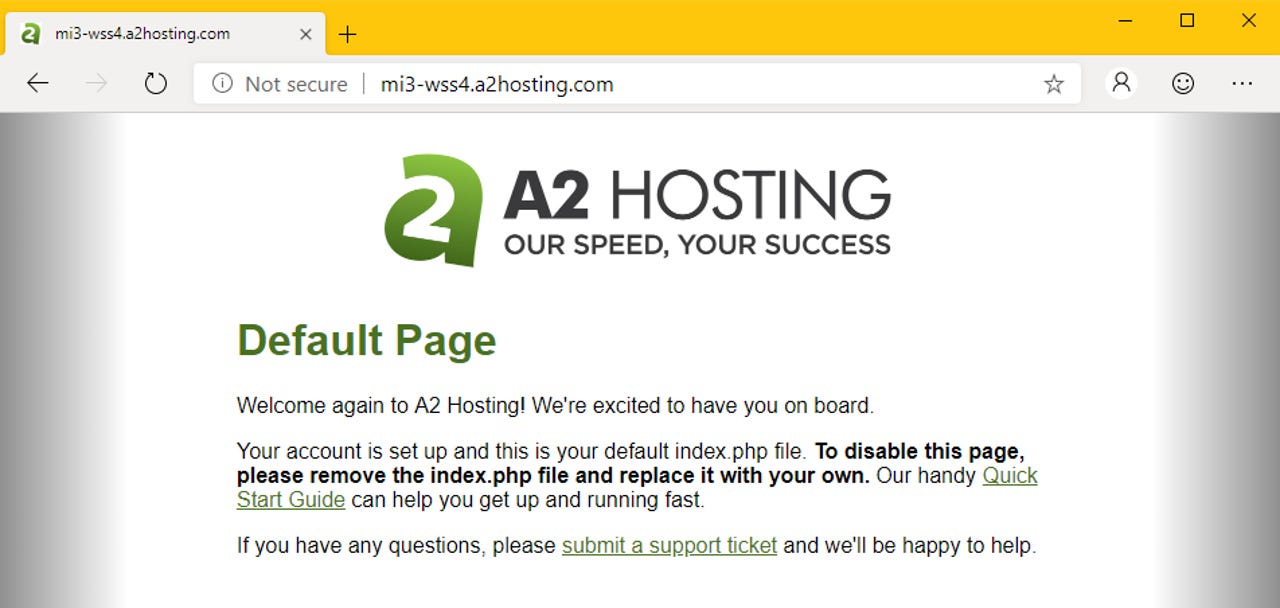
Impacted are all Windows-based servers owned by A2 Hosting, a provider of virtual private servers (VPS) and WordPress hosting services.
Customers losing money
The infection, which took place last week on April 23, has led to a week-long downtime that A2 staff has struggled to fix, leading to an unending stream of complaints and desperate pleas for help from customers bleeding money with each passing day of downtime.
No status updates since 29 April...no response to support tickets...no support chat online...194 hours of downtime and counting with zero communication from A2 and no real ETA on restored access to data. Come on A2, is this really the public image you want? pic.twitter.com/3PlnkNZvvR
— Ideal Technologies (@IdealMSP) May 1, 2019
"My business and all my hard work have been gutted within eight days by a hosting company that clearly did not have robust security in place," one of A2's customers told ZDNet today in an online conversation.
"Over the last eight days I have lost my Google [search] ranking which took me a year to achieve, and my customer base which was finally growing has been ruined," he said.
"Since the hack, A2 has provided zero information regarding my websites and database. I mean nothing, zero, zilch. I have been left to wait for an hour on hold calling support, to be told we understand your frustrations, but we cannot give you an ETA. They have this ridiculous update page, where nothing of substance is posted."
These complaints were similarly echoed by tens of other customers on social media, over the past week [1, 2, 3, 4, 5, 6, 7, 8, 9, 10].
GlobeImposter 2.0 is the most likely suspect
Based on currently available information, the ransomware infection appears to have snuck into A2's network via its Singapore-based data center and later spread to other Windows Server instances, also impacting the company's US operations.
Before A2 took all Windows servers down to avoid the ransomware from spreading to even more systems, some customers reported seeing files encrypted and renamed with a .lock extension.
From the A2, nothing. But I'm pretty sure about what happened. I was in a meeting with a customer, and we saw (yes, I've got witness) all my files (from my ftp area) were renamed to .lock and a message stating the area was attacked and encrypted.
— Marcos Romero ⓟ (@mcfromero) April 24, 2019
Based on the .lock file extension and the infection date, the ransomware appears to be a version of the GlobeImposter 2.0 ransomware strain, whose operators have been extremely active over the past weeks, Lawrence Abrams, malware analyst and founder of Bleeping Computer, told ZDNet today.
GlobeImposter, a ransomware strain known to be installd via RDP, may also be the reason why A2 has disabled RDP access to its servers after the attack.
Server restoration has been coming along slow
Security
The company has been unreachable since the incident, with all attempts to verify the ransomware attack with an A2 spokesperson failing as there was no direct line of communication. The company did not list an email for members of the media, the on-site chat widget redirected users to a status page, and all phone calls to a listed number ended up in being put on hold for tens of minutes, only to be asked to file a support ticket.
Nevertheless, the company has been working to restore some services (appears to be restoring from its own backups), although, not fast enough, as there are still tens of customers complaining about problems accessing servers even this week.
A status page suggests that Windows servers are up and running for US and EU customers, but the company's Singapore data center is still down for the count. But once the company finishes restoring services, it will also have to answer customer questions regarding possible data theft, as some customers now fear that attackers might have stolen some of their sensitive data before running the ransomware.
"If there is any message ZDNet can pass onto readers [...] is to back up regularly," an A2 customer who is still waiting to regain access to his website's data told us today. "It's never too late until it's too late. I will never not back up again."
A2's ransomware incident is just the latest in a long line of ransomware attacks that have seen new life over the last three months, after appearing to die down during the last quarter of 2018.
Past incidents include ransomware incidents at aluminum provider Norsk Hydro, cyber-security firm Verint, the UK Police Federation, utility vehicles manufacturer Aebi Schmidt, Arizona Beverages, engineering firm Altran, the Cleveland international airport, and chemicals producers Hexion and Momentive.
Updated on May 2, 5:00 am to add: The company has formally acknowledged the incident in a blog post. It said it was working with a leading third-party cybersecurity firm and law enforcement to investigate the event. Customers are still reporting downtime.
Free up disk space, remove malware, and tune up your Mac with CleanMyMac X
Related malware and cybercrime coverage:
- Dark web crime markets targeted by recurring DDoS attacks
- Why credit card data stealing point-of-sale malware is still such a big problem
- An inside look at how credential stuffing operations work
- Mysterious hacker has been selling Windows 0-days to APT groups for three years
- Recent Oracle WebLogic zero-day used to infect servers with ransomware
- Cartoon Network websites hacked to show Arabic memes and Brazilian male strippers
- How to avoid document-based malware attacks TechRepublic
- Game of Thrones has the most malware of any pirated TV show CNET