Chrome browser's 'secure' isn't the same thing as 'safe'

Google takes web security seriously. When the Google Chrome web browser encounters a payment site without Secure Socket Layer (SSL)/Transport Layer Security (TLS) encryption, it marks as insecure. Soon, Chrome will mark any HTTP site as insecure. That's great, but just because a site is tagged 'secure' doesn't mean it's safe.
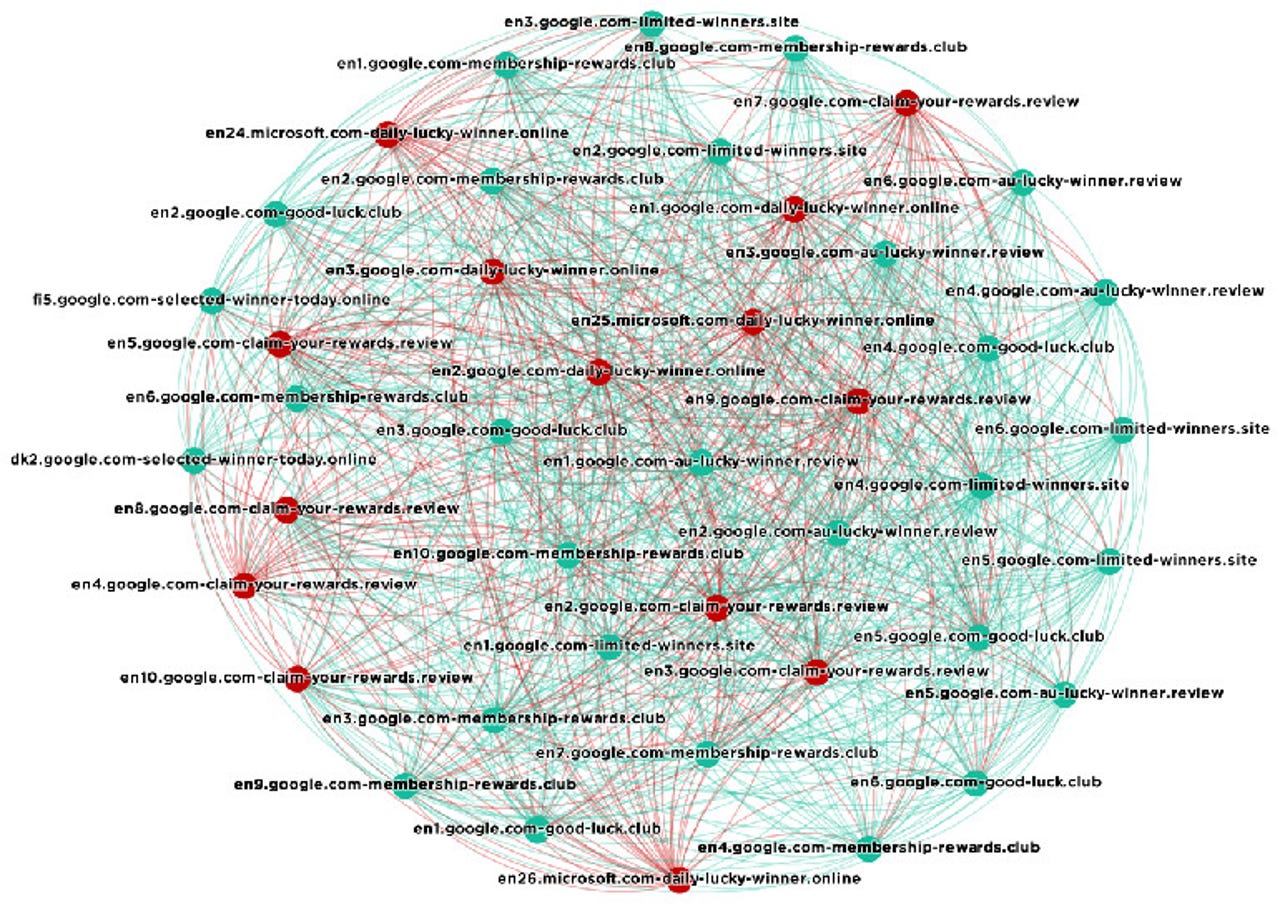
WordFence's analysis of phishing domains found many malicious domains -- those connected with red-lines sharing SSL certificates.
WordFence, a well-regarded WordPress security company, has found that SSL certificates are being issued by certificate authorities (CA) to phishing sites pretending to be other sites. Because the certificates are valid, even though they're operating under false premises, Chrome reports these sites as being secure. They're not.
Of course, CAs shouldn't issue bogus security certificates in the first place. Unfortunately, it happens.
Security
Lately, in a perfect example of "Why we can't have nice things," it's been revealed that the Let's Encrypt, the free, open, and automated CA, has been used to create thousands of SSL certificates for phishing sites illegally using "PayPal" as part of their name.
This problem isn't just with Let's Encrypt. For example, Symantec has been accused of being sloppy with issuing certificates. Let's Encrypt is, however, what the most common CA phishing sites are using now.
WordFence found PayPal wasn't the only one being abused. Fake certificates were being issued to sites pretending to be many popular companies such as Google, Microsoft, and Apple.
Google looks for fake sites, but, according to WordFence, "malicious sites that have been issued valid SSL certificates take some time to appear on Chrome's malicious site list." In short, "while the Safe Browsing project that Google runs does great work, Chrome users can not rely on it to reliably identify malicious sites and throw up a warning."
As WordFence explained: "In Chrome, when you see 'secure' in your browser location bar, it means that the connection between your browser and the website you are connected to is encrypted. ... It does not mean that the domain is 'trusted,' 'safe,' 'not malicious,' or anything else."
In addition, even when a "certificate is revoked once a CA realizes they should not have issued it, we show that Chrome still shows the site as 'secure.'" The 'revoked' status is only visible in Chrome developer tools. You can find it by using Chrome's View > Developer > Developer Tools menu on a suspicious site and then clicking View certificate.
Not spotting revoked certificates quickly isn't Google's fault. As Gibson Research has long pointed out, "Much of the certificate revocation system is badly broken and doesn't actually work!"
The easiest way to protect yourself from malicious sites is to check your web browser's location bar and read the full web site hostname that appears there. For example, a site that presented itself as an Apple site used the URL: https://secure5.apple.com-shop-account-signin.
The key is to look at the full hostname between 'https://' and before the next forward slash. If the URL continues on after the top-level domain (TLD name, such as .com, .net, or edu) and before the first forward slash, you're dealing with a fake site. Close your browser and never go to the site again.
Google and the CAs know about these problems. Google had no comment on this story, but I'm certain it is working on it. In the meantime, don't just click into a site because it looks secure. Maybe it is 'secure,' but it may not be in the least bit safe.
Related Stories:
- Chrome will soon mark some HTTP pages as 'non-secure'
- Symantec revokes faulty security certificates
- Google proposes sending Symantec to TLS sin bin
VIDEO: Google's 2016 web security report