Three serious Linux kernel security holes patched

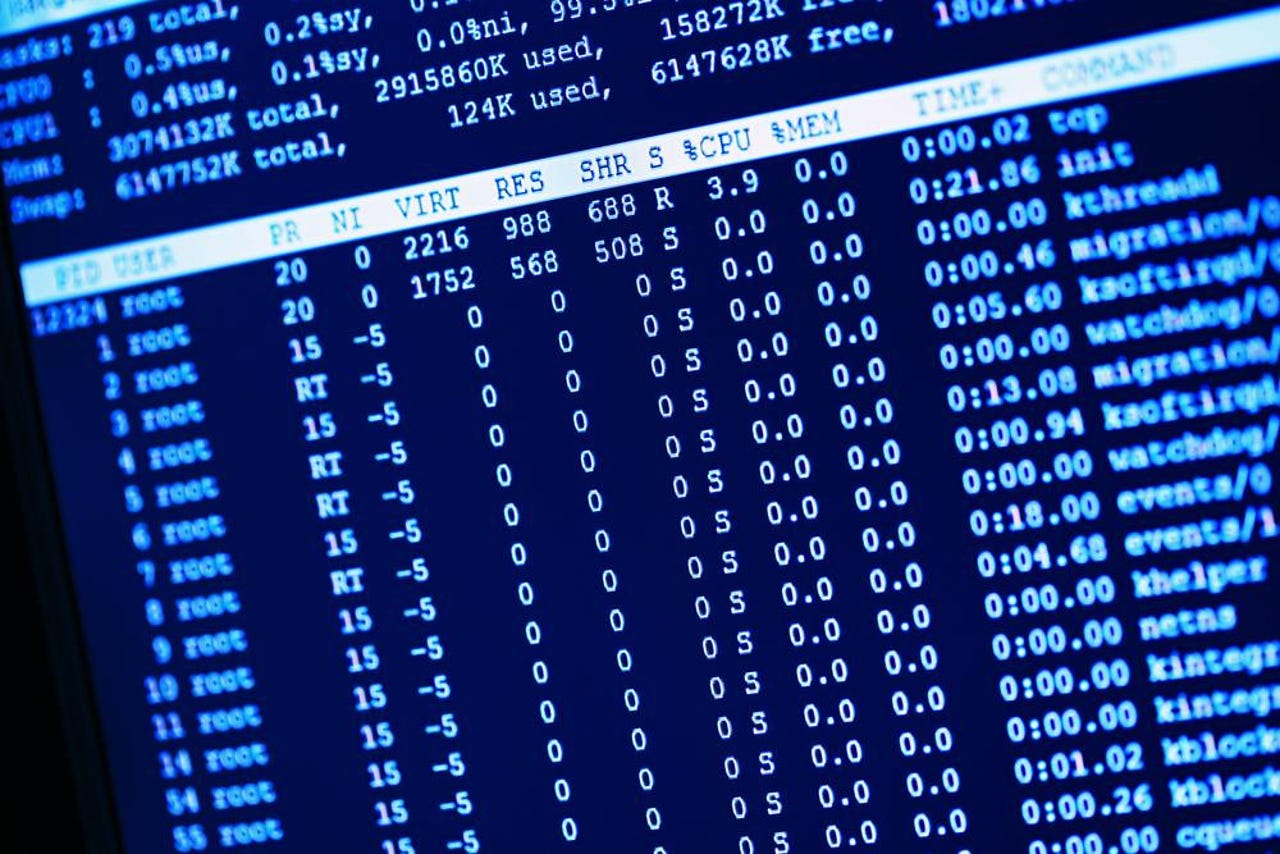
(Image: file photo)
The good news is developers are looking very closely at Linux's core code for possible security holes. The bad news is they're finding them.
At least the best news is that they're fixing them as soon as they're uncovered.
The latest three kernel vulnerabilities are designated CVE-2016-8655, CVE-2016-6480, and CVE-2016-6828. Of these, CVE-2016-8655 is the worst of the bunch. It enables local users, which can include remote users with virtual and cloud-based Linux instances, to crash the system or run arbitrary code as root.
Security
In short, it's nasty.
Philip Pettersson, a hacker and security researcher, found this bug. With it, a user can create a race condition in the Linux kernel's packet_set_ring function. A race condition happens when a system attempts to perform two or more operations simultaneously instead of one following the successful completion of the other.
To exploit this, a local user must first be able to create AF_PACKET sockets with CAP_NET_RAW in the network namespace. On many Linux distributions, but not all, an attacker can give themselves this ability by using unprivileged namespaces. Pettersson believes, with reason, unprivileged namespaces "should be off by default in all Linux distributions given its history of security vulnerabilities."
Operating systems that can be attacked by this include most newer versions of Debian, Fedora, Red Hat Enterprise Linux (RHEL) 7, and Ubuntu.
Pettersson has demonstrated that he can use this hole to create a root shell on Ubuntu 16.04 even when Supervisor Mode Execution Protection (SMEP) and Supervisor Mode Access Prevention (SMAP) have been deployed to protect the system.
The second security issue, CVE-2016-6480, also involves a race condition but it's not as serious. In this one, Adaptec AAC RAID controller driver can be used by a local attacker to crash a system.
Finally, CVE-2016-6828 can be used to break the Linux kernel's TCP retransmit queue handling code. This can be used to crash a vulnerable server or execute arbitrary code. It is, however, harder to use than Pettersson's discovery, so it's not as dangerous.
Be that as it may, you should patch your Linux system as soon as possible to avoid running into troubles. Patches are now available on all major Linux distributions.
Related Stories: