Tick, tock: Jigsaw ransomware deletes your files as you wait

A new breed of ransomware has ramped up the game in an evil way -- by threatening to delete user files if they refuse to give in and pay the ransom.
The malware, dubbed Jigsaw, is one of the latest entries into the ransomware family discovered by researchers.
Jigsaw, otherwise known as the originally labeled BitcoinBlackmailer.exe, was built on March 23 and was released into the wild only a week later. If a victim downloads the malware, the malicious code encrypts user files and sets up a locked screen in place of the desktop, in the usual manner of ransomware. Users are then held to ransom and are asked to pay a fee in virtual currency to retrieve their content.
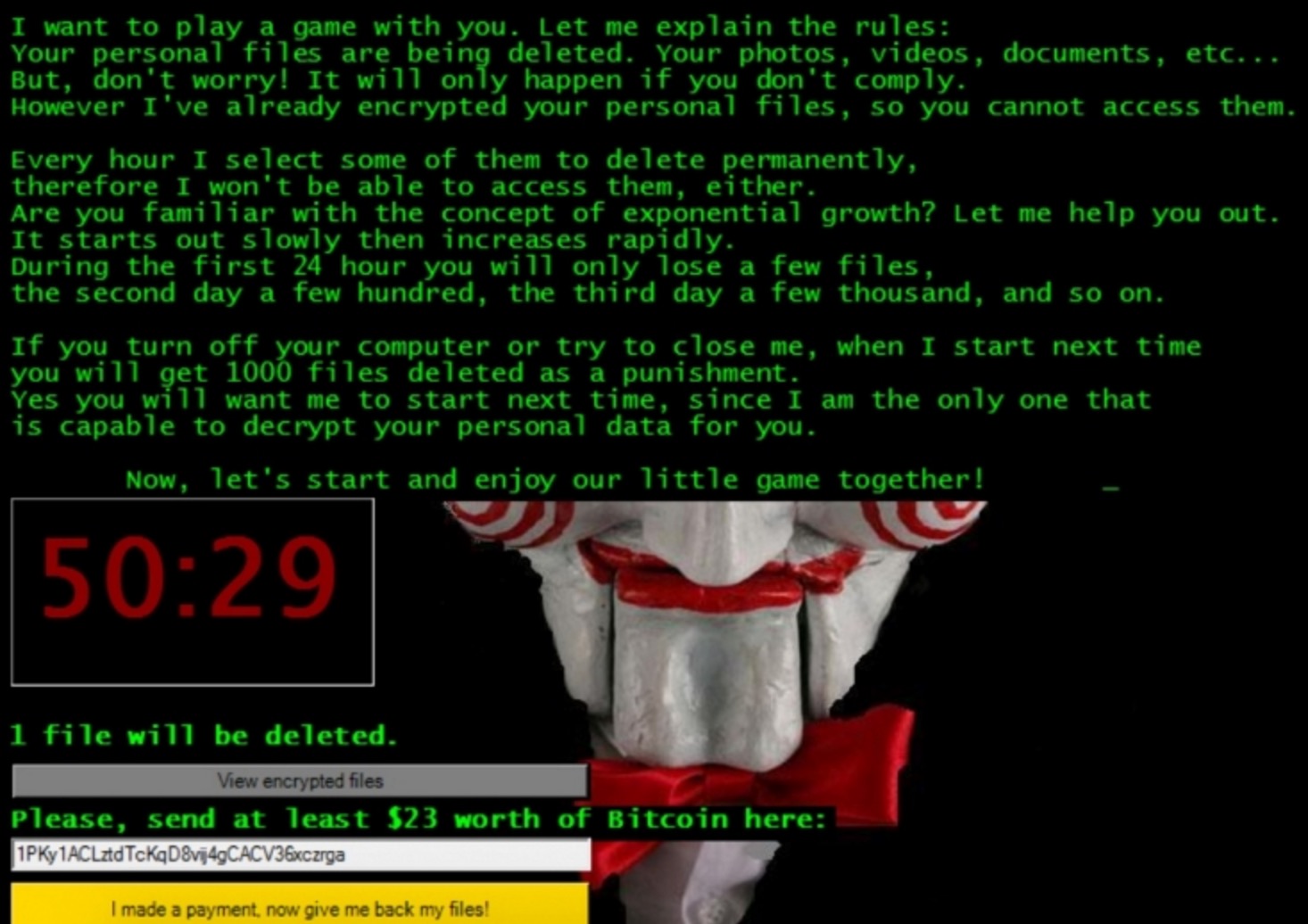
However, according to Forcepoint researchers, this ransomware not only encrypts files, but threatens users with a countdown. While displaying the face of Billy the Puppet from the horror movie Saw, victims are told files are selected by the hour for deletion if the ransom is not paid.
The threatening notice says that during the first 24 hours, only a few files will be deleted, but after this time, several thousand will be removed every day payment is missing. If users attempt to close the system or turn off the computer, Jigsaw tells users 1000 files will be deleted on startup "as a punishment."
However, the code is not exactly sophisticated. As Jigsaw is written in .NET, the team were able to reverse engineer the malware's code and rip out the encryption key used by Jigsaw to lock away user files -- as well as track down every one of the 100 Bitcoin addresses used to store ransomware payments.
In the video below, you can see how the ransomware behaves once a system is compromised -- and the creepy message victims are given to force them to pay up.
After extending their investigation of the malware, Forcepoint researchers said in an update the ransomware is being rebuilt and modified by different developers, which can make detection by antivirus software an issue.
The team was also able to discover where the Jigsaw is being sold. Timestamp clues led them to a Tor marketplace, where the malware is available for $139. At the time of writing, 24 people have purchased the code since early March. Despite the evil nature of the code, it seems that few are receiving a return on their investment -- at the moment.
Security
The firm traced four sample Bitcoin addresses and found that half were unsuccessful in securing a ransom payment, one was only $1 in Bitcoin -- likely to be a test -- and the last received only $89 in virtual currency.
Forcepoint says:
"A genius malware author this is not, the use of C#/.NET makes it trivial to reverse engineer and analyse. At the current rate, by selling the source code for the software is not going to generate nearly enough money to pay for much.
Finally, the customers who have purchased this kit are non too smart either, even with the documentation available some have left their names in the malware."
The infection rates are small and the return seems to be poor. However, the functionality of this new type of ransomware is still worth noting. As cybercrime becomes more sophisticated and tools are developed, even those with a lack of skill can cash in -- and Jigsaw is a prime example of how ransomware may end up evolving on a wider scale in the future.
Top tips to stay safe on public Wi-Fi networks
Read on: Top picks