Tor users 'not at risk' after failed attack by PlayStation, Xbox Live hackers

Tor, the anonymity network, is recovering this weekend after it was targeted by hackers.
The peer-to-peer network designed to keep users' and their activities anonymous from state surveillance was the subject of an attack, said to be launched by the same hackers who brought down Sony's PlayStation Network and Microsoft's Xbox Live services over the Christmas holiday.
In a statement on Friday, the Tor Project said the attack attempted to undermine the service by flooding it with fake servers.
"The attackers have signed up many new relays in hopes of becoming a large fraction of the network," the statement read. These new relay servers made up "less than 1 percent" of the Tor network's capacity during the attack, it added.
"We are working now to remove these relays from the network before they become a threat, and we don't expect any anonymity or performance effects based on what we've seen so far."
The Tor Project, a non-profit organization, warned on December 19 of an upcoming attack that may "attempt to incapacitate our network."
It's not clear if the two events are connected.
On Friday, hacker group Lizard Squad said on Twitter it would "no longer attack" online gaming services -- an attack it had claimed responsibility for, but had not been confirmed by others. Claiming to be armed with a Tor zero-day (an exploit that has not been previous made known) the group announced it would shift its efforts onto Tor.
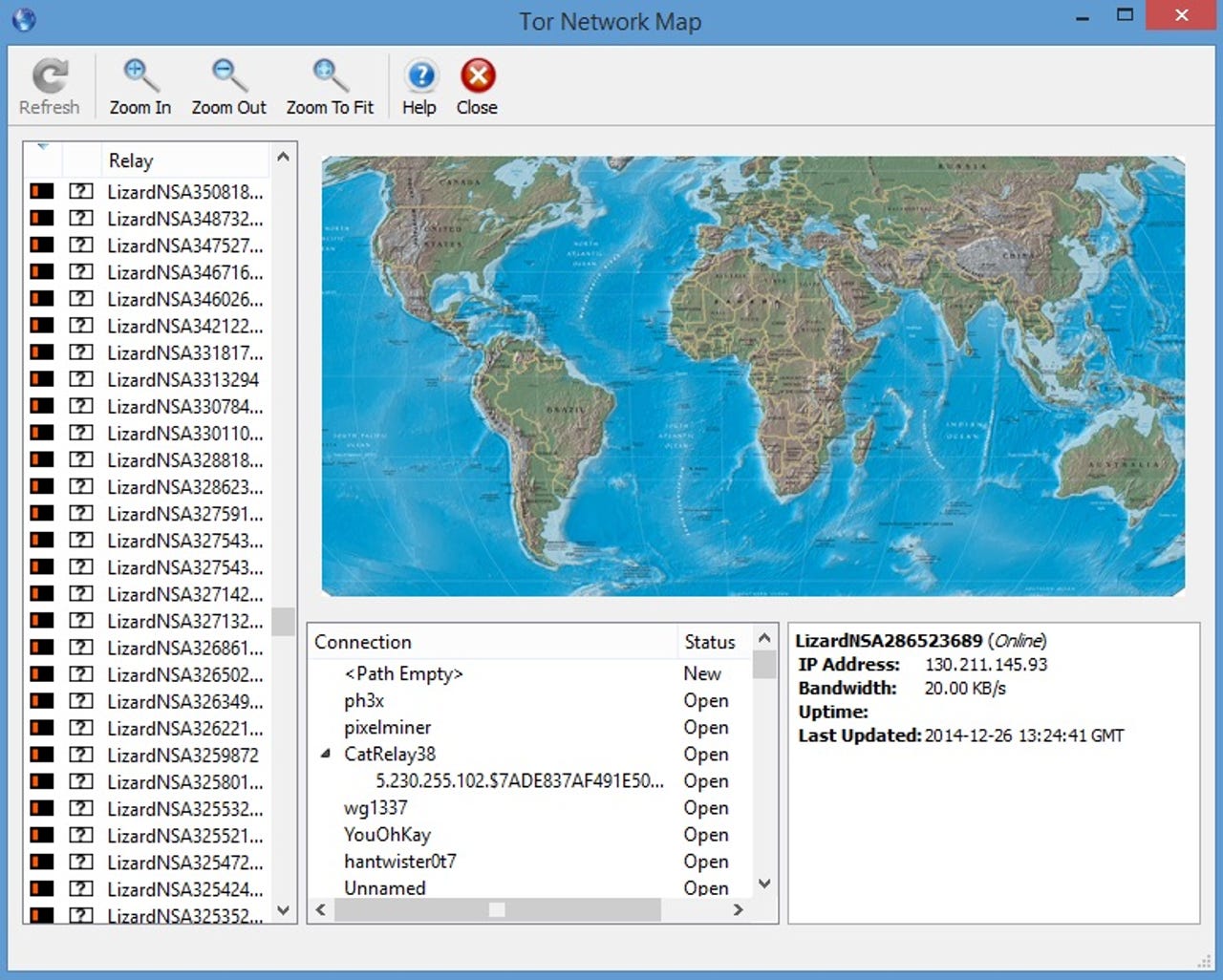
Within an hour 3,000 new nodes appeared on the Tor network, all named "LizardNSA."
The hackers' motives are not clear. However, in one tweet, the hackers said: "Only hackers, miscreants and pedophiles use Tor." Activists and journalists in particular regularly use Tor, known for providing anonymity to its users, to evade surveillance in oppressive states. Criminals also use the service to evade law enforcement.
Though we only have the Lizard Squad's word that it was behind the shutdown the online gaming services over the weekend, it's looking increasingly likely that it is behind the unsuccessful attack on Tor.
Security researcher Frederic Jacobs said in an email that the new Tor nodes started on Google's cloud service.
"The fact that they are all in the same IP address space is preventing them to deanonymize users because clients are picking relays in different address spaces," he explained.
Google did not immediately return emails for comment. (The company is currently on its holiday break.)
In his calculations, the Tor network could not have passed anonymized data through enough of the compromised nodes for a user's identity or activity to be denonymized.
The design of Tor's open-source network, which initially had funding from the U.S. Dept. of Defense and is still regularly used by governments today, requires relays to stay in the network for "at least three days" before the network grants them greater bandwidth, Cryptocat developer and security expert Nadim Kobeissi explained.
Kobeissi said the attack seemed potentially dangerous at first, but the attack failed to gain any significant weight due the use of new, and low bandwidth servers, he confirmed in an email, following comments he made on Twitter.
Security
Privacy and security researcher Runa Sandvik, who previously worked at the Tor Project, explained in an email that the service could have been at risk if the hackers used higher bandwidth relays that had been accepted into the service.
In this case, the hacker group's setup would not have worked, she said.
Tor has a built-in feature to "ensure that the relays joining the network are stable and offer enough bandwidth to be useful," Sandvik explained. A new relay on Tor goes through a number of phases to ensure that it is reliable and secure, the project's blog explained in a September 2013 post.
However, had the Tor Project not have taken swift action to remove the rogue nodes from its network, the anonymity of "a majority of Tor users" would have eventually been at risk from having their activities tracked, Kobeissi said.
When reached for comment, the Tor Project did not comment beyond its written statement.