Two-thirds of iOS apps disable ATS, an iOS security feature

Security
Two-thirds of iOS apps do not use an Apple technology that can help them support and enforce encrypted communications, according to a report published today by cyber-security firm Wandera.
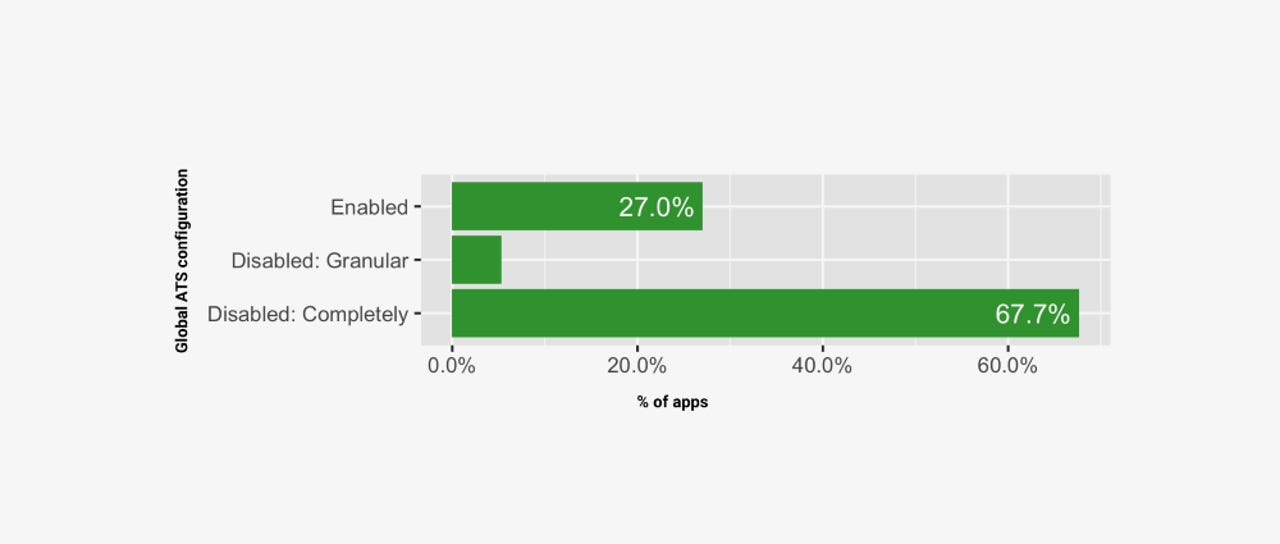
The company said it scanned over 30,000 iOS applications and found that 67.7% of the apps were disabling a default iOS security feature called ATS (App Transport Security) on purpose.
ATS was introduced with the release of iOS 9, released in September 2015, and works by blocking all HTTP connections between an app and its remote server.
At the WWDC 2016 conference, Apple announced plans to make ATS obligatory for all iOS apps starting January 2017, but the company abandoned its plans in December 2016, weeks before the enforcement was to take force.
ATS still ships enabled by default for all iOS apps, and developers must disable it when they are coding their apps, in case they need to talk to HTTP domains or some error-prone HTTPS websites that may default back to HTTP -- and trigger an ATS ban.
In its report, Wandera says that only 27% of the 30,000 apps it scanned are currently using ATS to enforce encrypted communications and block plaintext HTTP connections.
Around 5.3% use ATS, but they disabled it granularly, for certain domains.
Ad frameworks recommend disabling ATS
According to Wandera, the reason why three years later the ATS security feature has seen little adoption appears to be that ad frameworks/networks often recommend in their documentation that iOS developers disable ATS inside apps, to prevent iOS from blocking communications to ad servers in case of an error.
"Ad network operators are in a competitive space and want to streamline the process for developers to make their apps compatible," Wandera said. "By removing 'roadblocks' such as encryption requirements, they make it easier for more developers to incorporate their ad networks into their applications."
This seems to be the primary reasons why ATS is often disabled. For example, Wandera said that ATS is more widely used inside paid apps, which do not rely on advertising revenue, and where app developers have no reason to disable ATS to safeguard their profits.
Some paid apps still disable ATS, but this appears to be related to content management, with some app makers wanting to make sure remotely-hosted content on HTTP or error-prone HTTPS gets loaded without glitches.
Furthermore, these percentages should be taken with a grain of salt, as ATS being disabled doesn't necessarily mean that those iOS apps are not using HTTPS.
"It just means that system safeguards are disabled and hence there is much more room for [HTTPS] error," the Wandera team said.
Apple WWDC 2019 keynote: Scenes and surprises
Related cybersecurity coverage:
- I2P network proposed as the next hiding spot for criminal operations
- Hollywood lie: Bank hacks take months, not seconds
- Only 5.5% of all vulnerabilities are ever exploited in the wild
- Apple announces 'Sign in with Apple' feature
- New Iranian hacking tool leaked on Telegram
- Wave of SIM swapping attacks hit US cryptocurrency users
- iOS developers still failing to build end-to-end encryption into apps TechRepublic
- The best identity theft monitoring services for 2019 CNET