Uber patches security flaw leading to subdomain takeover

Uber has patched a security flaw which allowed attackers to compromise its sign-on service and left subdomains vulnerable.
Security
Security researcher Arne Swinnen disclosed the details of the exploit this week after Uber resolved the problem. According to the security expert, Uber was vulnerable to subdomain takeover due to the Single Sign-On (SSO) system at auth.uber.com, as well as session and cookie hijacking.
Swinnen says the problem lay within the SSO, which was based on shared cookies between all *.uber.com subdomains. If one subdomain was compromised and cookies were stolen, this left all of them exposed -- potentially escalating the breach to authentication bypass on the full system and all subdomains protected by it, such as vault.uber.com, partners.uber.com, and riders.uber.com.
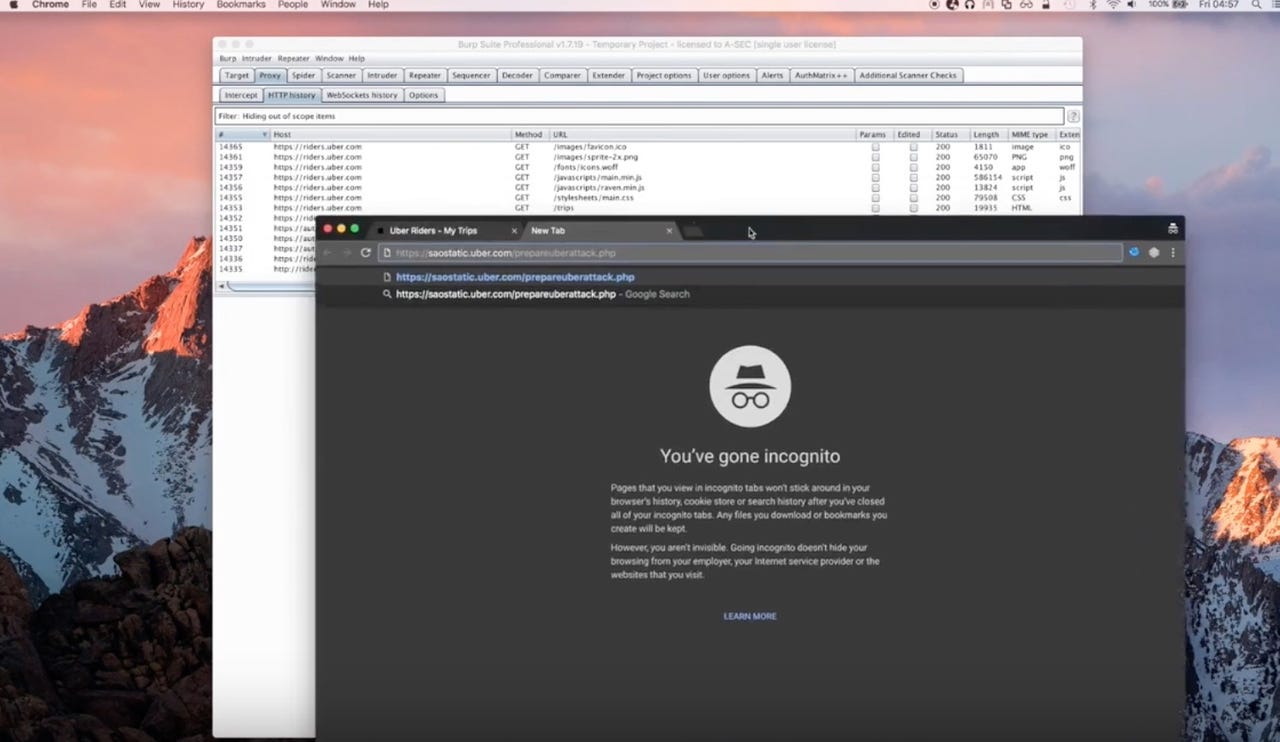
The saostatic.uber.com pointed to an Amazon Cloudfront CDN via a DNS CNAME, however, the hostname was not registered there. This allowed Swinnen to quickly take over this domain.
Now this domain was compromised as Uber forgot to remove this record, the researcher was then able to steal valid session cookies through SSO due to cookie sharing.
"Uber did have some countermeasures in place to prevent this, but these were bypassed and reported together with the subdomain takeover for increased impact," Swinnen said. "Any compromised *.uber.com subdomain could be used to perform the same attack, although Uber explicitly mentioned several *.uber.com subdomains as out of scope in their bug bounty program policy at the time of reporting."
In order to circumvent some of Uber's protective controls, an attacker is still able to gain victim session tokens -- should the target be logged into auth.uber.com -- by luring them to visit a web page under control by the attacker. Once these credentials have been stolen, attackers are able to impersonate the victim on Uber domains.
Swinnen included proof-of-concept (PoC) code in his disclosure.
The security flaw was first reported to Uber on April 7, to be triaged three days later. After a week, the ride-hailing service offered the researcher the $500 minimum bug bounty payout -- however, as Swinnen still owned saostatic.uber.com two months later, he pinged the company.
It was only on June 6 that Uber began triaging the issue, saying that the report "fell through the cracks."
On June 7, the DNS CNAME record for this subdomain was removed and within another week, Swinnen was awarded an additional $4,500.
In July, Uber deployed an additional IP address check to make sure the vulnerability was no longer an issue.
See also: Uber uses artificial intelligence to figure out your personal price hike
In related news, last week Google parent company Alphabet dropped a series of patent claims levied against Uber in an intellectual property theft lawsuit.
While this is good news for Uber investors which have had to deal with everything from claims of sexism and a toxic culture, former CEO Travis Kalanick's escapades and a constant battle with traditional taxi services worldwide, Alphabet has clarified in a recent conference call that the battle isn't over.
While the case is still going to trial, Alphabet agreed with the court's request that the patent claims be dropped from 100 instances to only ten.