How to lock up your digital life and privacy in an hour (in pictures)

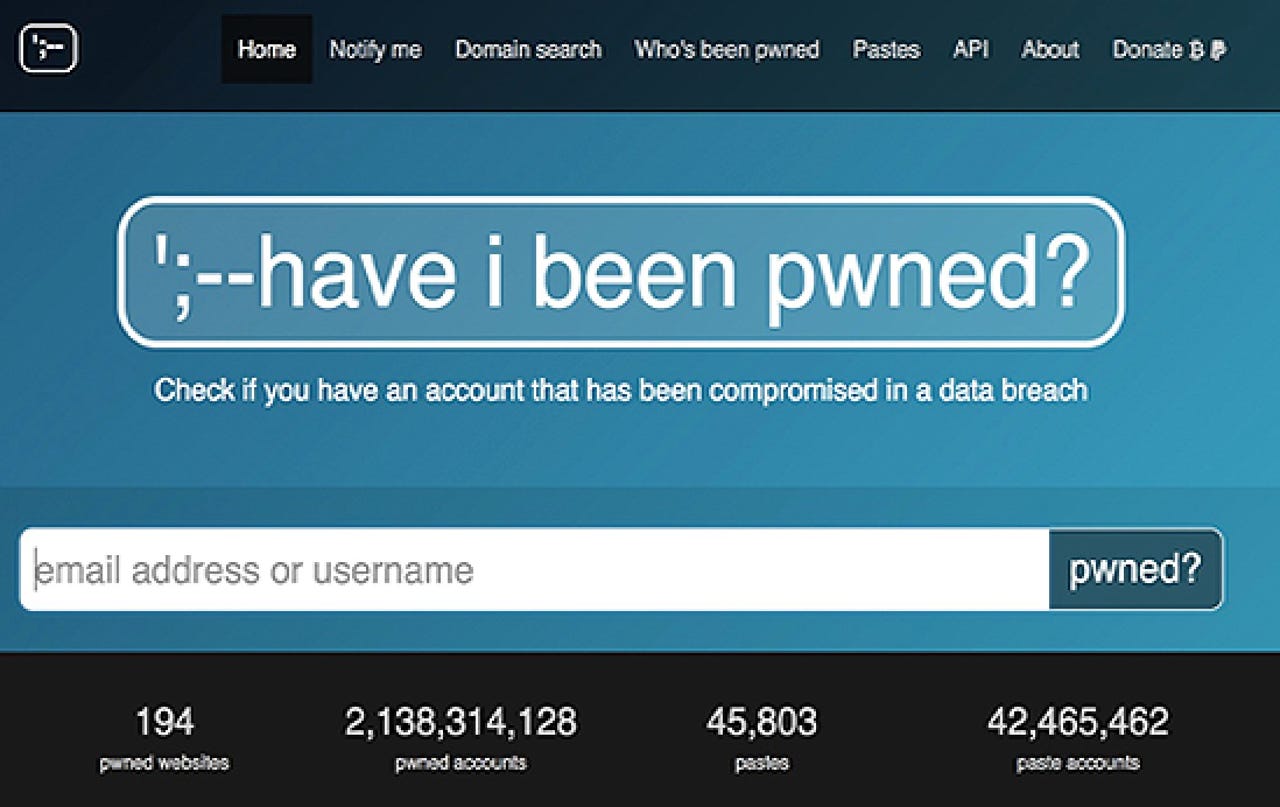
Haveibeenpwned
It is worth knowing whether or not you are already compromised. By submitting your email address to Troy Hunt's Haveibeenpwned search engine, you can see whether or not any accounts linked to your email addresses have been caught up in data breaches and whether or not your account information has been found in public paste documents online, which may have been sold or leaked to the public.
Change your passwords
If any of your accounts have been compromised or even if it has been a while since you've changed your credentials, you should certainly at least take the time to secure the most important ones with a fresh set.
Password lockers such as LastPass can take the stress out of remembering long, complex passwords, and you should make sure that at the least, none of your main accounts -- such as email services, Amazon, and social networks -- are using repeat phrases. If one is compromised, that could mean the rest of them are, too.
Two-factor verification
It may be a hassle, but introducing two-factor verification on your most frequently used accounts is worthwhile. 2FA will send a code to your mobile device when login attempts are made, which adds an additional layer of security for attackers to crack.
The system, now available on major services including Google's Gmail, Facebook, Twitter, and PayPal, takes a little time to implement but can be very important in protecting your privacy. Yubikey is also an option if you would like to harden your credentials through hardware.
Enable 2FA for:
HTTPS Everywhere
The EFF's HTTPS Everywhere is a browser extension for the Firefox, Opera, and Chrome web browsers. It takes no more than a few seconds to download, and once installed, will encrypt communication between yourself and major websites that have not yet introduced encryption by default.
By keeping these channels secure, cyberattackers will have a harder time spying on you and conducting attacks which could redirect you to fake websites.
Lock up your devices
It might seem a simple thing, but placing some kind of lock -- whether a PIN code or biometric fingerprint -- on your mobile devices can improve your privacy not only by preventing casual access, but giving you time to change your passwords and details for online accounts in the case of theft.
Try to stay away from easy codes such as "1234" and finger patterns that can be worked out quickly, if possible.
Turn off location tracking
On most mobile devices there will be a 'location tracking' or 'GPS' option displayed in settings menus. While some apps including mapping technologies and weather updates, need this geolocation data to run properly, whenever you do not have need of it -- turn it off. There is no need for your mobile device to track your location unless absolutely necessary and it takes mere seconds to turn off the service.
Turn on automatic updates
Whether you are using a Windows PC, Mac, or Android smartphone, automatic updates are crucial to protecting your privacy. These over-the-air (OTA) updates will often contain security fixes for vulnerabilities which attackers can exploit to compromise your device, and so it is worth keeping them on to keep yourself as protected as possible.
If you haven't changed the default settings, you don't need to do anything.
Malware scanning
While Internet browsers will often pick up suspicious files and malicious websites, by occasionally using a malware scanner, you can make sure that no malicious code such as spyware, adware, and more problematic Trojans, worms, and viruses are lurking on your system and potentially compromising everything you do.
Recommendations for free, lightweight software: Malwarebytes | AVG | Panda
Update your social media account privacy settings
If you want to keep your content for friends' eyes only and want to block and keep others from viewing pictures, images, and videos, as well as stay off search engines, it is worth taking a few minutes to make sure your social network privacy settings are as you want them.
You can change settings including profile visibility, hiding messages, share content with specific groups of people and take control of others linking you to their content.
Have some time left?
If you have some additional time to spare, you can also take the time to set up a secondary email address. When signing up for online services, you are sometimes asked to receive third-party information and will be added to subscriber lists. To help keep your inbox clear, it may be worth setting up a free account to keep these message volumes under control.
For a more extensive privacy boost, it may also be worth the time to setup an email address left wholly unconnected with you purely for accounts which need your financial information, such as Amazon, delivery services, and online banking. That way, should your main email account become compromised, you are keeping the financial keys away.