West African banks hit by multiple hacking waves last year

Banks and financial institutions in West Africa have been hit by four different hacking campaigns last year, according to a report published today by US cyber-security giant Symantec.
Security
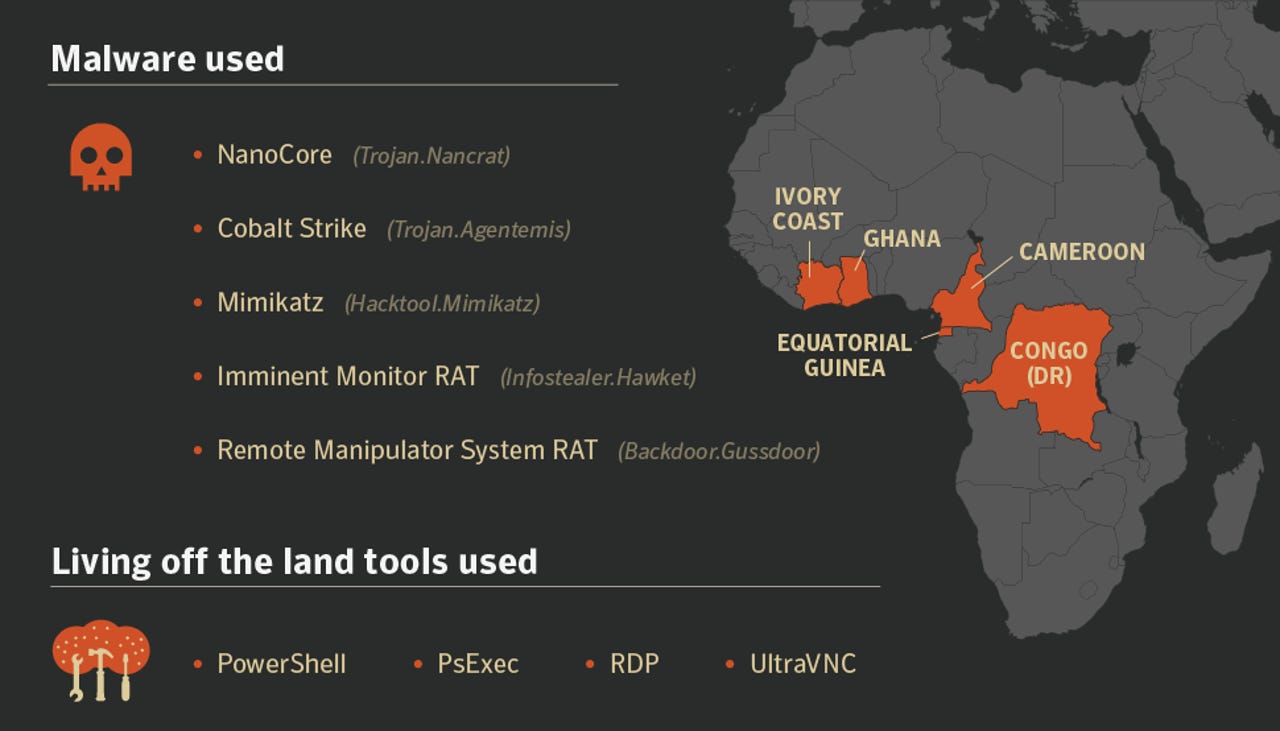
Organizations in Cameroon, Congo (DR), Equatorial Guinea, Ghana, and the Ivory Coast have been hit, Symantec said today.
The attacks, which haven't yet been attributed to any hacking group, in particular, have used low-end malware strains and applications natively found on Windows systems (a tactic known as "living off the land").
The malware used in these attacks is the kind you find shared for free online, or anyone can buy via dedicated websites or from hacking forums.
The list includes Cobalt Strike (a pen-testing framework repurposed as a modular backdoor), Mimikatz (a pen-testing tool repurposed as a password stealer), and the NanoCore, Imminent Monitor, and Remote Manipulator System, all three being remote access trojans (RATs).
On top of these, Symantec says that hackers also used local tools such as PowerShell (a native Windows scripting utility), PsExec (a Microsoft Sysinternals tool used for executing processes on networked systems), and Windows RDP (a native Windows utility for connecting to remote Windows systems via a desktop-like interface). Attackers also deployed UltraVNC, an open-source remote administration tool that some companies' system administrators install so they can connect and manage remote systems, a-la TeamViewer, PsExec, or RDP.
Below is a summary of the four different hacking campaigns that Symantec saw aimed at West African banks and financial institutions last year. The company isn't yet sure if they've been carried out by the same group, or not.
| Campaign | Tools | Countries | Start |
| 1 | NanoCore, PsExec | Ivory Coast and Equatorial Guinea | Mid-2017 |
| 2 | PowerShell, Mimikatz, UltraVNC, Cobalt Strike | Ivory Coast, Ghana, Congo (DR), and Cameroon | Late 2017 |
| 3 | Remote Manipulator System RAT, RDP, Mimikatz | Ivory Coast | - |
| 4 | Imminent Monitor RAT | Ivory Coast | December 2018 |
While some readers might be surprised by the focus on attacking African banks, this is, actually, a trend that many industry experts saw coming.
Over the past two years, there have been concerted efforts from different hacking crews, some of Russian and some of North Korean origin, that have focused on banks and financial institutions located in South East Asia, Eastern Europe, and South America.
Experts from multiple cyber-security firms pointed out that the reasons banks are targeted in these regions are because there's a high chance that not all invested in their IT infrastructure and cyber-security measures. A poorly designed and unsupervised network makes attacks easier to carry out and hacks easier to hide for long periods of time, compared to an attack aimed at banks located in Western Europe or North America.
Lacking from reports from the past years was Africa, which surprisingly hasn't been targeted until now, according to Symantec.
Unfortunately, the African financial sector's period of calm appears to be over.
Indicators of compromise for these recent attacks are available in Symatec's report, here.
Cybercrime and malware, 2019 predictions
More cybersecurity news:
- North Korean hackers infiltrate Chile's ATM network after Skype job interview
- G Suite update warns you when someone is exporting your company's data
- US charges Ukrainian for SEC 2016 hack, others for insider trading
- Hackers breach and steal data from South Korea's Defense Ministry
- Liberian ISP sues rival for hiring hacker to attack its network
- Hacker 'BestBuy' sentenced to prison for operating Mirai DDoS botnet
- Google now lets you donate to charity through the Play Store CNET
- Phishing and spearphishing: A cheat sheet for business professionals TechRepublic