WinRAR versions released in the last 19 years impacted by severe security flaw

Samsung Unpacked
WinRAR, one of the world's most popular Windows file compression applications, has patched last month a severe security flaw that can be abused to hijack users' systems just by tricking a WinRAR user into opening a malicious archive.
The vulnerability, discovered last year by security researchers from Check Point Software, impacts all WinRAR versions released in the last 19 years.
On its website, the WinRAR team boasts of having a userbase of over 500 million users, all of whom are most likely impacted. The good news for all WinRAR users is that WinRAR devs released an update to fix the issue last month.
According to a Check Point technical write-up that takes a deep dive into WinRAR's inner workings, the vulnerability resides in the UNACEV2.DLL library included with all WinRAR versions.
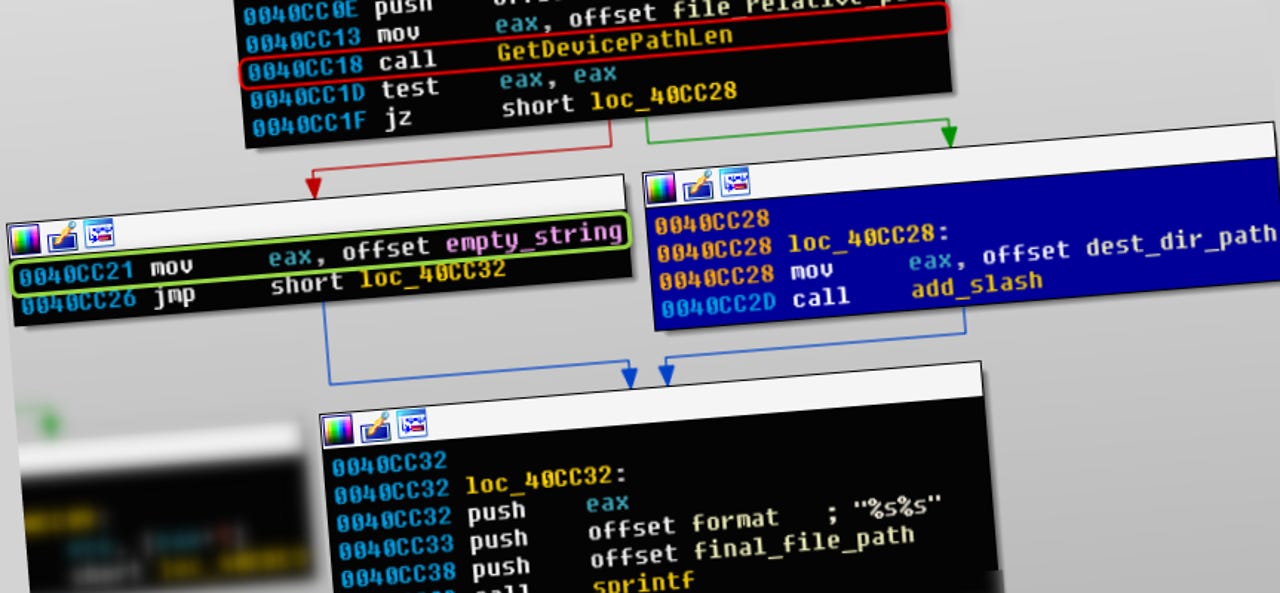
This library is responsible for unpacking archives in the ACE format. Check Point researchers discovered a way to build malicious ACE archives that when decompressed used coding flaws in this library to plant malicious files outside the intended decompression path destination.
For example, Check Point researchers were able to use this vulnerability to plant malware in a Windows PC's Startup folder, malware that would execute after the next reboot, infecting and taking over the PC. A proof-of-concept demo video recorded by the Check Point team is available below.
WinRAR devs released WinRAR 5.70 Beta 1 on January 28 to address this vulnerability --tracked under the CVE-2018-20250, CVE-2018-20251, CVE-2018-20252, and CVE-2018-20253 identifiers.
Because devs lost access to the UNACEV2.DLL library source code around 2005, they opted to drop support for ACE archive formats altogether.
In the coming months and years, because of WinRAR's extremely large userbase, users should be aware that malware operators will most likely attempt to exploit this vulnerability.
Home users should take care not to open any ACE archives they receive via email unless they've updated WinRAR first. System administrators at large corps should also warn employees about opening these files without having updated WinRAR first, as well.
Exploit vendors have already shown interest in buying vulnerabilities in file compression utilities last year, offering to pay as much as $100,000 for a remote code execution flaw in WinRAR, 7-Zip, WinZip (on Windows) or tar (on Linux).
The reason is that these types of apps are almost always installed on corporate or home computers, and are an ideal attack surface for hackers or government entities.
We're still paying up to $100,000 for #0day exploits (code execution) affecting major file archivers: WinRAR, 7-Zip, WinZip (on Windows) or tar (on Linux). For more information: https://t.co/fKnggJyb0H #BigBounties
— Zerodium (@Zerodium) October 18, 2018
Many of 2018's most dangerous Android and iOS security flaws still threaten your mobile security
Related security coverage:
- Microsoft removes eight cryptojacking apps from official store
- White hats spread VKontakte worm after social network doesn't pay bug bounty
- Rietspoof malware spreads via Facebook Messenger and Skype spam
- Another WordPress commercial plugin gets exploited in the wild
- New macOS security flaw lets malicious apps steal your Safari browsing history
- Malvertising campaign hits US users hard over Presidents' Day weekend
- Cryptomining malware spread via US, UK and Australian government sites TechRepublic
- Google bans cryptocurrency mining extensions for Chrome CNET