Death of the internet: GIF at 11

People have been talking about the internet crashing for as long as there has been an internet. The use of the 1980s graphic format "GIF" for the common phrase used to describe "Death of the internet: GIF at 11" tells you that. We've always been scared of it, but today it's a real possibility.
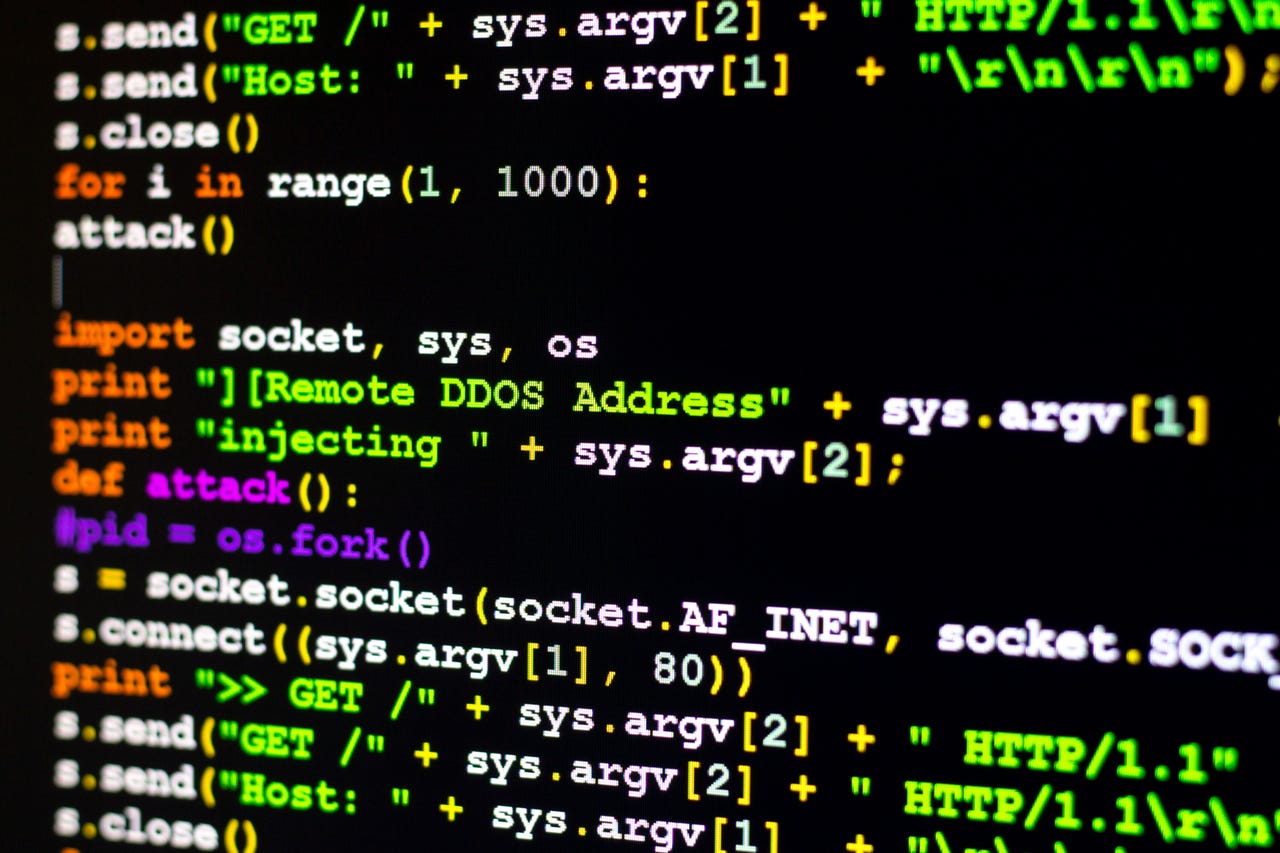
Unbeknown to you, your home connected devices could be unwitting participants in a DDoS attack. Your ISP, however, can spot and stop them... if they really wanted to.
In fact, I'm certain we'll see such an attack. If I were a betting man, I'd say we'll see it sometime around November 8th: The US elections date.
An attack then would make a huge impression. And, as noted security expert Bruce Schneier pointed out recently, "over the past year or two, someone has been probing the defenses of the companies that run critical pieces of the internet. These probes take the form of precisely calibrated attacks designed to determine exactly how well these companies can defend themselves, and what would be required to take them down. We don't know who is doing this, but it feels like a large nation state. China or Russia would be my first guesses."
The US is already investigating Russian cyberattacks designed to influence the 2016 election. Why not a massive attack on the US's internet infrastructure just in time for the election?
Schneier continued that major internet companies are telling him they're seeing an increase in [Distributed Denial of Service] DDoS attacks against them. "Moreover, they have seen a certain profile of attacks. These attacks are significantly larger than the ones they're used to seeing. They last longer. They're more sophisticated. And they look like probing. One week, the attack would start at a particular level of attack and slowly ramp up before stopping. The next week, it would start at that higher point and continue. And so on, along those lines, as if the attacker were looking for the exact point of failure."
That's not just what he'd been told. Internet security firm Verisign is reporting DDoS activity that's the highest it's ever seen.
It's only getting worse.
In late September, prominent security expert Brian Krebs had his security blog, Krebs on Security, blown off the Internet by a DDoS attack that came to a mind-boggling 665Gbps. Akamai, the content delivery network (CDN), counts attacks of over 100Gbps as being "Mega attacks." This attack, on a single individual's website, was six times that size.
Akamai and its DDoS prevention division Prolexic was forced to give up trying to handle the attack on Krebs. They couldn't afford to keep trying to keep his site up against a perfect storm of SYN Floods, GET Floods, ACK Floods, POST Floods, and GRE Protocol Floods bogus email subscriptions and garbage Skype requests. Today, Krebs on Security is back up on Alphabet's Project Shield, Google's experimental anti-DDoS service.
Attacks over 100Gbps are becoming commonplace. Massive DDoS attacks can now be done by any script kiddie.
Here's the worst news. Truly massive attacks are easier than ever to make.
It doesn't take a nation to blow away a site. Roland Dobbins, an Arbor Networks principal engineer, told Krebs, "When it comes to DDoS attacks, nation-states are just another player. Today's reality is that DDoS attacks have become the Great Equalizer between private actors & nation-states."
How? With the Internet of Things (IoT).
Krebs sourly noted it didn't require a James Bond villain. "This attack was launched with the help of a botnet that has enslaved a large number of hacked so-called IoT devices -- mainly routers, IP cameras, and digital video recorders (DVRs) that are exposed to the internet and protected with weak or hard-coded passwords."
The botnet code used to make the attack, Mira, has been dumped on the web. That was a few days ago. In a few weeks, script kiddies can start making 500Gbps+ attacks.
Wonderful.
So, what can you do about it? Not much in the short-run. In the long run, programmer Stephen Satchell suggests that the US Consumer Product Safety Commission (CPSC) require IoT vendors for everything from washers to routers to secure their devices after any use in a DDoS attack. It's his hope that by making manufacturers legally responsible for the damage caused by their devices, they'll finally take security seriously.
Security
I like the idea, but I'm not holding my breath. Security takes expertise and money.
Another idea, which could be implemented more quickly, is for internet service providers (ISPs) and router and switch vendors to finally implement Network Ingress Filtering, better known as BCP-38.
BCP-38 was proposed in 2000 when DDoS attacks were first becoming a serious problem. It works by filtering out bogus internet addresses. Another internet proposal, Ingress Filtering for Multihomed Networks, BCP-84, helps to make it possible to use.
They're not perfect, but they would go a long way to reducing DDoS attacks to manageable sizes.
So why wasn't it implemented a decade ago? Andrew McConachie, an ICANN technical and policy specialist, explained in an article that ISPs are too cheap to pay the small costs required to implement BCP-38.
Their logic is, McConachie explained, "It costs money to install filters, albeit a very small amount, but it is not free. Nor is the labor capable of installing those filters cheap. Therefore it makes economic sense for this network operator to not install filters. No one is DDOSing their network, that's someone else's problem."
It's not. It hasn't been someone else's problem for years now. And now it's on the brink of becoming everyone's problem in the worst possible way. Besides, it doesn't cost that much. McConachie said "any carrier grade [Border Gateway Protocol] BGP router can support many more Access Control Lists (ACLs) than are actually needed to support implementation of BCP 38".
Are you an internet engineer or do you want to help solve the problem rather than explain to your customers why their internet went dead in the water? Check into the Routing Resilience Manifesto, consider joining the IETF SAVI working group, or visit the Anti-Spoofing start page.
The tools are out there to save the internet. We must use them before it's too late.
This isn't paranoid fantasy. This is our future unless we act now.
Related Stories: