Image Gallery: June's cyber threat landscape
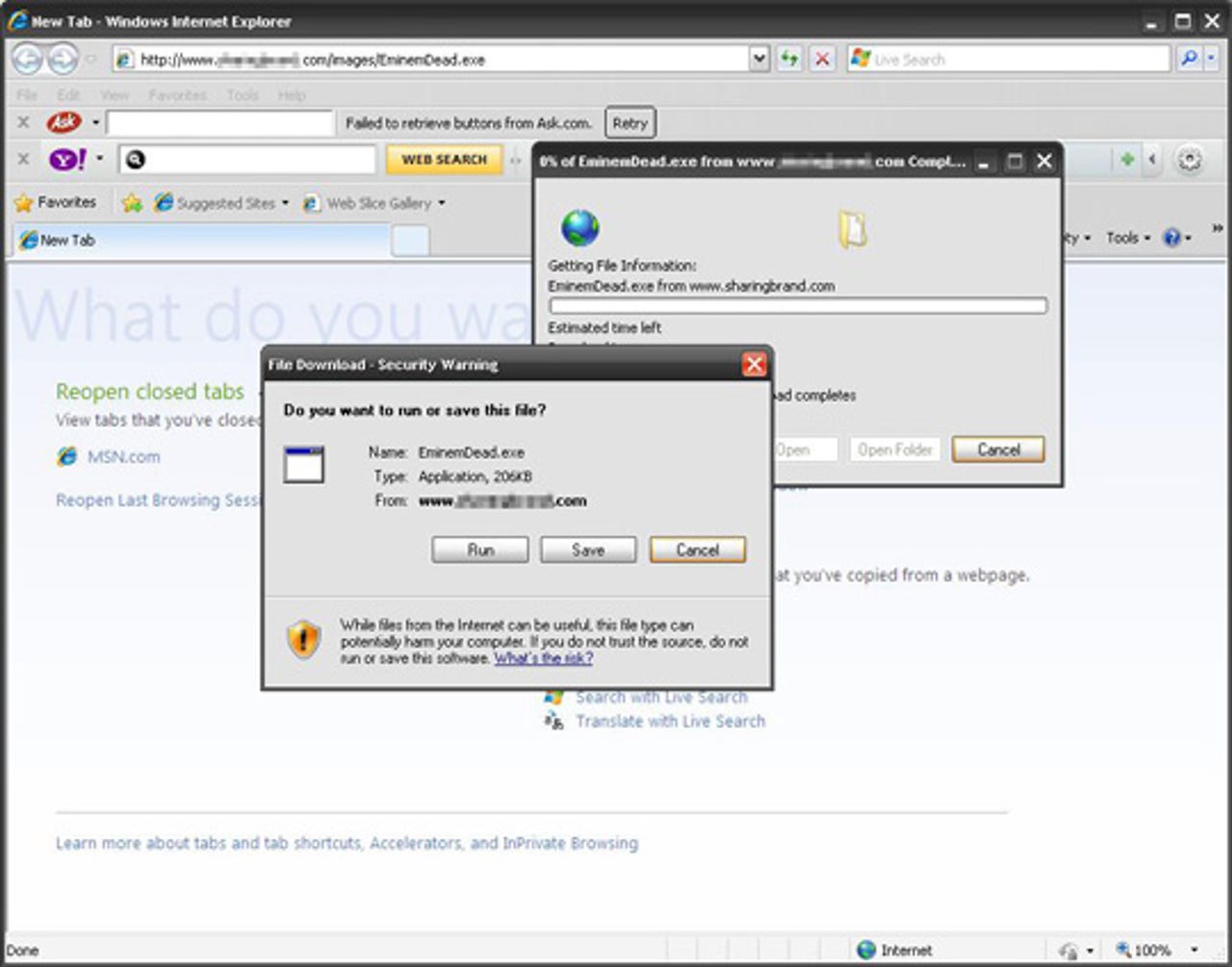
Image Source: Fake News of Eminem’s Death Leads to Malware
Related: Protection tips for the upcoming FIFA World Cup themed cybercrime campaigns
Image Source: The security and privacy ramifications of AT&T's iLeak
Image Source: Malware Watch: Adobe zero day attack, malicious FIFA-themed spam, exploit serving Virus Alerts
Is It Legal To Buy OEM Software?
Image Source: FIFA World Cup Scams Continue to Circulate
Image Source: Inside the Carding Underworld
Image Source: Inside the Carding Underworld
Image Source: Dissecting the Exploits/Scareware Serving Twitter Spam Campaign
Image Source: Dissecting the Exploits/Scareware Serving Twitter Spam Campaign
Image Source: Dissecting the Ongoing U.S Federal Forms Themed Blackhat SEO Campaign - Part Two
Image Source: Dissecting the Ongoing U.S Federal Forms Themed Blackhat SEO Campaign - Part Two
Image Source: The EFF releases new HTTPS Everywhere Firefox extension
Image Source: Facebook Photo Album Themed Malware Campaign, Mass SQL Injection Attacks Courtesy of AS42560
With Facebook increasingly getting abused by clickjacking campaigns, it's worth taking a peek into the traffic these campaigns generate. This image shows the disturbingly high click-through rate for a sampled campaign, clearly demonstrating that the potential for abuse is there. For the latest security news, cyber threats and malware incidents, visit the Zero Day blog
Image Source: Dissecting the 100,000+ Scareware Serving Fake YouTube Pages Campaign
Image Source: Dissecting the 100,000+ Scareware Serving Fake YouTube Pages Campaign
Yet another variation of the fake "Your Computer is Infected" scareware window, seen in blackhat search engine optimization (blackhat SEO) campaigns. For the latest security news, cyber threats and malware incidents, visit the Zero Day blog
Image Source: FIFA World Cup Scams Continue to Circulate
Image Source: Facebook users clickjacked by the 101 Hottest Women in the World
Image Source: Malware Watch: Twitter password reset emails, IRS-themed crimeware, malicious PDFs, and fake YouTube pages
In June, researchers from Intego discovered the OSX/OpinionSpy spyware in 29 free Mac OS X screensavers. For the latest security news, cyber threats and malware incidents, visit the Zero Day blog
Image Source: Malware Watch: Free Mac OS X screensavers bundled with spyware
Image Source: Vendor of Mobile Spying Apps Drives Biz Model Through DIY Generators
Fraudulent online gambling propositions, continue getting spammed, with the spammers earning revenue using an affiliate program. For the latest security news, cyber threats and malware incidents, visit the Zero Day blog
Image Source: Exploit.PDF-Dropper.Gen
Image Source: Is It Legal To Buy OEM Software?
Image Source: It's signed, therefore it's clean, right?
Image Source: Malware Watch: Skype exploit, Skype-themed malicious spam campaigns detected
Professionally designed scam sites like this one, continue tricking tens of thousands of uses into purchasing Rolexes for $500, even less. For the latest security news, cyber threats and malware incidents, visit the Zero Day blog
Image Source: Dissecting the Exploits/Scareware Serving Twitter Spam Campaign
Image Source: Dissecting the Exploits/Scareware Serving Twitter Spam Campaign
Image Source: Malware Watch: Twitter password reset emails, IRS-themed crimeware, malicious PDFs, and fake YouTube pages
Image Source: Targeted Attacks with Excel Files
Image Source: Malicious Notification Spam: Account Verification
Image Source: FIFA World Cup Used to Lure Victims in Targeted Attack
Related: Inside an affiliate spam program for pharmaceuticals
Related: Inside an affiliate spam program for pharmaceuticals