Windows Vista's Firewall offers false sense of security
Now, with Microsoft Windows Vista in the market, it is a good time to start looking at its resilience to people and code that would just assume do your system harm. In Windows Vista, Microsoft's built in firewall took a step forward from the one offered in Windows XP by offering outbound blocking. But does it get the job done? Not quite.For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post post in ZDNet's TestBed blog.

1 of 23 Matt Conner/ZDNET
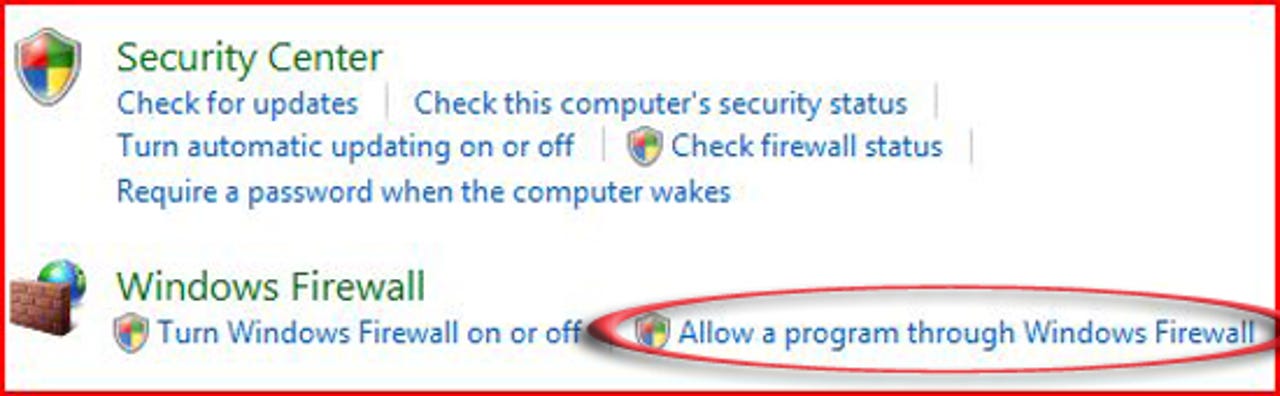
Knowing that Windows Vista's firewall is capable of outbound blocking, but that it wrongfully defaults to let all programs access the Internet when it should let none, we were looking for an intuitive way to correct the problem. After going into Windows Vista's Control Panel, the link that said "Allow a program through Windows Firewall" made the most sense to us. As a side note, we were logged in with administrator privileges during this test.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
2 of 23 Matt Conner/ZDNET
After clicking on the link to allow a program through the firewall, we received this warning dialog. It's a good warning because, in the event that something else like malware started the program, the user would be warned of the attempted start before Windows Vista allows it. We clicked the "Continue" button.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
3 of 23 Matt Conner/ZDNET
On the subsequent Windows Firewall Setting dialog, there weren't too many visual cues for someone looking to configure the firewall for outbound blocking. The "General" tab offered us the ability to block all incoming connections which is not what we wanted. So, intuition led us to the "Exceptions" tab on top.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
4 of 23 Matt Conner/ZDNET
Tried as we did, we could not make sense of what the Windows Firewall Exceptions tab is trying to tell us. We were looking for something (anything!) that said "If you're looking for information on outbound block, you've arrived!" But the following text didn't tell us much:
Exceptions control how programs communicate through Windows Firewall. Add a program or port exception to allow communications through the firewall..
In our attempt to read between the lines, we assumed that since the list includes programs that are already on the computer and the text says "allow communications through the firewall," that this meant "programs on the computer trying to communicate through the firewall" (in other words, like cars going through a tollbooth, outbound communications). But, as you will see, we were quite mistaken. We clicked on the "Properties" button in hopes that we might get some more detail, but....(see the next image)...
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
Exceptions control how programs communicate through Windows Firewall. Add a program or port exception to allow communications through the firewall..
In our attempt to read between the lines, we assumed that since the list includes programs that are already on the computer and the text says "allow communications through the firewall," that this meant "programs on the computer trying to communicate through the firewall" (in other words, like cars going through a tollbooth, outbound communications). But, as you will see, we were quite mistaken. We clicked on the "Properties" button in hopes that we might get some more detail, but....(see the next image)...
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
5 of 23 Matt Conner/ZDNET
... when we saw the resulting dialog (this time for "Core Networking"), it was of little or no help. But then we saw the "How do I view and edit all properties?" link and thought "Eureka, we've finally found it!".... Unfortunately...(see the next image)..
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
6 of 23 Matt Conner/ZDNET
..(continued from previous image) while the subsequent Frequently Asked Questions and a healthy list of questions and answers, the one question we just clicked on didn't appear on the list. *sigh*. Not only that, there were absolutely no references to outbound blocking. (double *sigh*). But we did see one question, the answer to which were hoping would solve the first mystery: "What does allowing a program through a firewall mean?" Recall that we saw that in one of the first configuration dialogs and we weren't sure if it meant inbound blocking, outbound blocking, or both.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
7 of 23 Matt Conner/ZDNET
Equally unhelpful was this explanation which tells us that it's about bidirectional blocking. Yet so far, we've seen nothing... not even a clue...as to how, for each program on that list we saw previously, to granularly configure inbound and outbound blocking independently of each other. Or, by adding a program to the list, does Vista simply block in both directions automatically and that's all there is to it? As it turns out, that's not the case. We know because we did a little test (next)
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
8 of 23 Matt Conner/ZDNET
We conducted our test on a brand new Lenovo Thinpad X60 Tablet and so we thought we'd first see what happens if we select an existing application like the Lenovo Registration applet....
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
9 of 23 Matt Conner/ZDNET
We added some tint to this because it wasn't easily visible in the screenshot. But this just shows how we clicked on the Lenovo Registration applet...(you can see how the path to the application below at the bottom changed to reflect this selection).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
10 of 23 Matt Conner/ZDNET
To turn the Lenovo Registration applet into one of the "excepted" applications, we checked it on the exceptions list. At this point, we realized that, by adding a new application and checking it, we didn't learn anything different than we did when inspecting the properties of the one that was already checked (Core Networking). So, we decided to install another application (Firefox) -- one that was easy to tell if there was any outbound blocking going on --- to see what would happen.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
11 of 23 Matt Conner/ZDNET
In this screenshot, we just finished downloading Firefox 2 and now we're getting ready to install it (note that in previous screenshots, you can see that they were taken after Firefox was installed.. we didn't realize until after we did a few things that we needed to get screenshots of them too!).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
12 of 23 Matt Conner/ZDNET
Once installed, Vista stopped us from running Firefox until we manually approved it. That's a good idea because, like with our attempt to run the firewall configuration tool, the computer has no way of knowing whether the user at the keyboard launched the software, or if some other software (potentially malware) launched it. So, with this safety feature, it doesn't matter who launched it. The user has to approve the launch.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
13 of 23 Matt Conner/ZDNET
Immediately after launching for the first time, Firefox retrieves a Web page from the Mozilla Web site which confirms our understanding that, by default, applications are not blocked from sending information through the firewall and out to the Internet (outbound blocking would have stopped this). We think this is a bad default behavior and that the way it should behave is that everything should be blocked by default and then allowed on an exception basis.
We went back to the firewall exception list and checked off Firefox to see if that would invoke outbound blocking, but it was to no avail (leading us to believe it the exceptions list must be for inbound blocking).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
We went back to the firewall exception list and checked off Firefox to see if that would invoke outbound blocking, but it was to no avail (leading us to believe it the exceptions list must be for inbound blocking).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
14 of 23 Matt Conner/ZDNET
Although the standard configuration interface for Vista's firewall offers no obvious clues as to where to go in order to configure outbound blocking, it actually appears in a different part of Windows Vista (we're still not sure why we didn't intuitively know that the configuration dialogs for the outbound firewall wouldn't be under the standard entry point for the firewall). Anyway to get to the more granular controls for the firewall, you first go to Vista's Control Panel and then you click on "System and Management"....
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
15 of 23 Matt Conner/ZDNET
Then, although there are no visual cues that it's hiding under there, the next thing to click on is the "Administrative Tools" link. Trust us, this is really the way to managing outbound blocking on Vista's firewall (yes, we know, by now you're saying "This can't be for real")...
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
16 of 23 Matt Conner/ZDNET
There, on the bottom of the list is "Windows Firewall and Advanced Security." We're warning you though. If you are a mortal Windows user (like most), what you will see next may frighten you.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
17 of 23 Matt Conner/ZDNET
This is what the top level screen looks like after diving into the Windows Firewall and Advanced Security area of Windows Vista. None of the items in the center are clickable. But the text that says "Outbound connections that do not match a rule are allowed" make it quite clear that all outbound connections are allowed unless a user defined rule explicitly prevents it. We were hoping we could click on that (or right click on it) and flip it to the opposite status (where everything is disallowed unless a rule explicitly allow it), but we couldn't. So, we clicked on "Outbound rules" (top left)
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
18 of 23 Matt Conner/ZDNET
Here, Windows Vista is showing us the existing outbound blocking rules. These were either put there by Microsoft (this is a brand new installation of Vista) or Lenovo (it's a new Thinkpad that came with Vista pre-installed). We decided to experiment with creating a new rule. The goal was to block Firefox from accessing a specific Web site. We didn't get very far (and we don't think other mortals will either).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
19 of 23 Matt Conner/ZDNET
We started by clicking on "New Rule" (top right)
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
20 of 23 Matt Conner/ZDNET
After clicking on "New Rule" on the "Outbound Rules" display, we were offered four types of rules: Program, Port, Predefined, and Custom. Since we just wanted to block Firefox, we picked "Program." We expected a list of programs like the exceptions list we saw in the Windows other firewall configuration tool. But, that's not exactly what we got next.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
21 of 23 Matt Conner/ZDNET
Hey, you want to screw up a machine really quickly? Then give people access to Windows' System32 directory by default. We were hoping to get a list of programs that we could create some outbound blocking rules for. Instead, we were dumped into the Windows System32 directory. We knew our way around from here, but we're relatively certain most Windows users would be completely lost if asked to, from this starting point, hunt down the actual executable file that maps to the program that needs outbound blocking.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
22 of 23 Matt Conner/ZDNET
We also tried the "port" path from the Rule Type dialog. Nope. No user friendliness here. In fact, not even for experienced people. For example, look at the drop down list of protocols. Some of the key ones you'd hope to find there like HTTP and FTP aren't on list. Anyway, we can't imagine mortals looking at this user interface. Next, we tried going down the "Custom" path.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
23 of 23 Matt Conner/ZDNET
Finally, we went down the custom path hoping that once we picked Firefox, that we could be selective about what Internet domains Firefox could access. As you can see from the buried dialog box, we were hoping to answer the question of which remote IP addresses to include in the rule with a domain instead of an IP address. We could run a trace to the domain to get the IP address, but the physical IP address could change. Working off domain would be better. Sometimes, where we've been instructed to enter an IP address, domain has worked. So, we tried it here (but with no luck as you can see). This led us to some sage advice for you: be sure to tell grandma to jot down her most despised IP addresses before configuring the outbound blocking on her Windows firewall. Better yet, just tell her to get a firewall from another security vendor (and disable the Windows one).
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
For David Berlind's write-up on Vista's inadequate personal firewall, see his blog post in ZDNet's TestBed blog.
Related Galleries
Holiday wallpaper for your phone: Christmas, Hanukkah, New Year's, and winter scenes
![Holiday lights in Central Park background]()
Related Galleries
Holiday wallpaper for your phone: Christmas, Hanukkah, New Year's, and winter scenes
21 Photos
Winter backgrounds for your next virtual meeting
![Wooden lodge in pine forest with heavy snow reflection on Lake O'hara at Yoho national park]()
Related Galleries
Winter backgrounds for your next virtual meeting
21 Photos
Holiday backgrounds for Zoom: Christmas cheer, New Year's Eve, Hanukkah and winter scenes
![3D Rendering Christmas interior]()
Related Galleries
Holiday backgrounds for Zoom: Christmas cheer, New Year's Eve, Hanukkah and winter scenes
21 Photos
Hyundai Ioniq 5 and Kia EV6: Electric vehicle extravaganza
![img-8825]()
Related Galleries
Hyundai Ioniq 5 and Kia EV6: Electric vehicle extravaganza
26 Photos
A weekend with Google's Chrome OS Flex
![img-9792-2]()
Related Galleries
A weekend with Google's Chrome OS Flex
22 Photos
Cybersecurity flaws, customer experiences, smartphone losses, and more: ZDNet's research roundup
![shutterstock-1024665187.jpg]()
Related Galleries
Cybersecurity flaws, customer experiences, smartphone losses, and more: ZDNet's research roundup
8 Photos
Inside a fake $20 '16TB external M.2 SSD'
![Full of promises!]()