Most home routers don't take advantage of Linux's improved security features

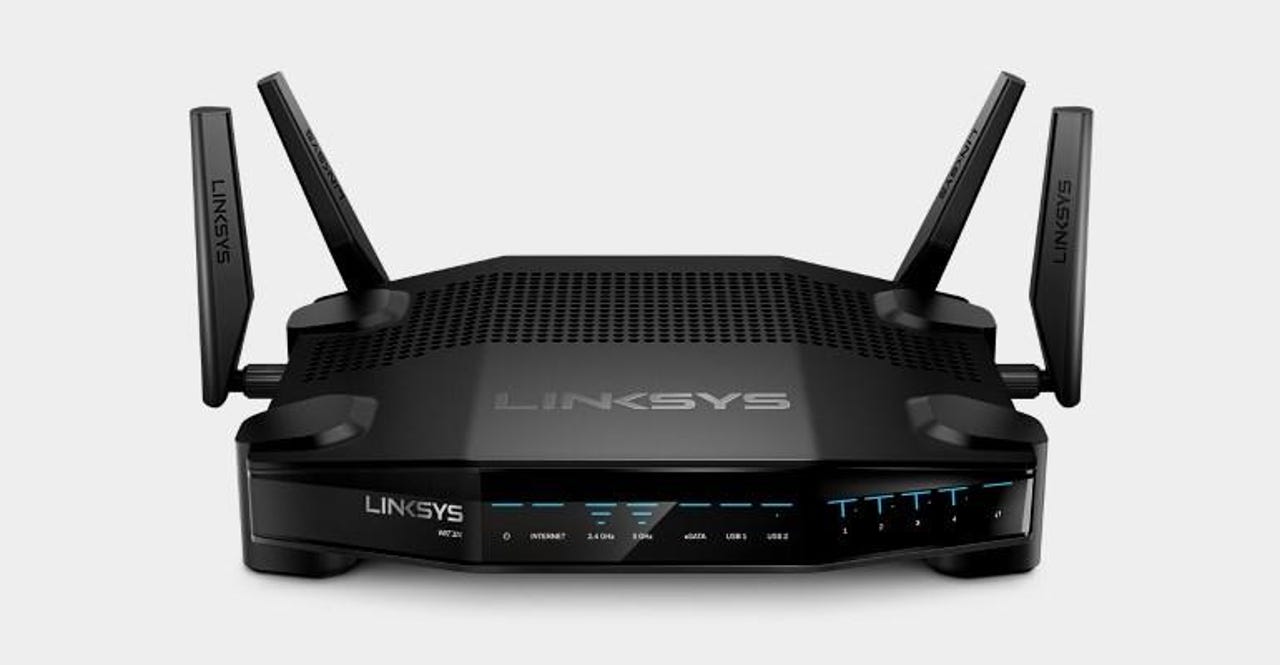
Linksys WRT32X, the router that scored the highest in the Cyber-ITL security-focused case study.
Many of today's most popular home router models don't take full advantage of the security features that come with the Linux operating system, which many of them use as a basis for their firmware.
Security hardening features such as ASLR (Address Space Layout Randomization), DEP (Data Execution Prevention), RELRO (RELocation Read-Only), and stack guards have been found to be missing in a recent security audit of 28 popular home routers.
Security
Security experts from the Cyber Independent Testing Lab (Cyber-ITL) analyzed the firmware of these routers and mapped out the percentage of firmware code that was protected by the four security features listed above.
"The absence of these security features is inexcusable," said Parker Thompson and Sarah Zatko, the two Cyber-ITL researchers behind the study.
"The features discussed in this report are easy to adopt, come with no downsides, and are standard practices in other market segments (such as desktop and mobile software)," the two added.
While some routers had 100 percent coverage for one feature, none implemented all four. Furthermore, researchers also found inconsistencies in applying the four security features within the same brand, with some router models from one vendor rating extremely high, while others had virtually no protection.
According to the research team, of the 28 router firmware images they analyzed, the Linksys WRT32X model scored highest with 100 percent DEP coverage for all firmware binaries, 95 percent RELRO coverage, 82 percent stack guard coverage, but with a lowly 4 percent ASLR protection.
The full results for each router model are available below. Researchers first looked at the ten home routers recommended by Consumer Reports (table 1), but then expanded their research to include other router models recommended by other news publications such as CNET, PCMag, and TrustCompass (table 2).
Test results for Consumer Reports recommended routers
Test results for CNET, PCMag, TrustCompass recommended routers
As a secondary conclusion of this study, the results also come to show that the limited hardware resources found on small home routers aren't a valid excuse for failing to ship router firmware without improved security hardening features like ASLR, DEP, and others.
It is clear that some companies can ship routers with properly secured firmware, and routers can benefit from the same OS hardening features that Linux provides to desktop and server versions.
Last but not least, the study also showed an inherent weakness in routers that use a MIPS Linux kernel. The Cyber-ITL team says that during their analysis of the 28 firmware images (ten of which ran MIPS Linux and 18 of which ran ARM Linux) they also discovered a security weakness in MIPS Linux kernel versions from 2001 to 2016.
"The issue from 2001 to 2016 resulted in stack based execution being enabled on userland processes," the researchers said --issue which made DEP protection impossible.
The 2016 MIPS Linux kernel patch re-enabled DEP protection for MIPS Linux, researchers said, but also introduced another bug that allows an attacker to bypass both DEP and ASLR protections. Researchers detailed this MIPS Linux bug in more detail in a separate research paper available here.
Handy hardware for the home office
More cybersecurity news:
- Hackers dump data of hundreds of German politicians on Twitter
- Security researcher cracks Google's Widevine DRM (L3 only)
- New ReiKey app can detect macOS keyloggers
- Google Chrome flaw patched three years after initial report
- Hacking attacks on your router: Why the worst is yet to come
- USB Type-C gets authentication to protect against malicious devices
- Why router-based attacks could be the next big trend in cybersecurity TechRepublic
- Security researchers find flaws in chips used in hospitals, factories and stores CNET