Scammers abused Apple developer program to steal millions from victims on Tinder, Bumble, Grindr, Facebook Dating

Sophos has released a new report this week about a dating app scam that led to the theft of millions of dollars from people on Tinder, Bumble, Grindr, Facebook Dating and similar apps.
After gaining their trust on these dating apps, scammers convinced victims to download fake crypto apps, where they duped them into investing money before freezing the accounts.
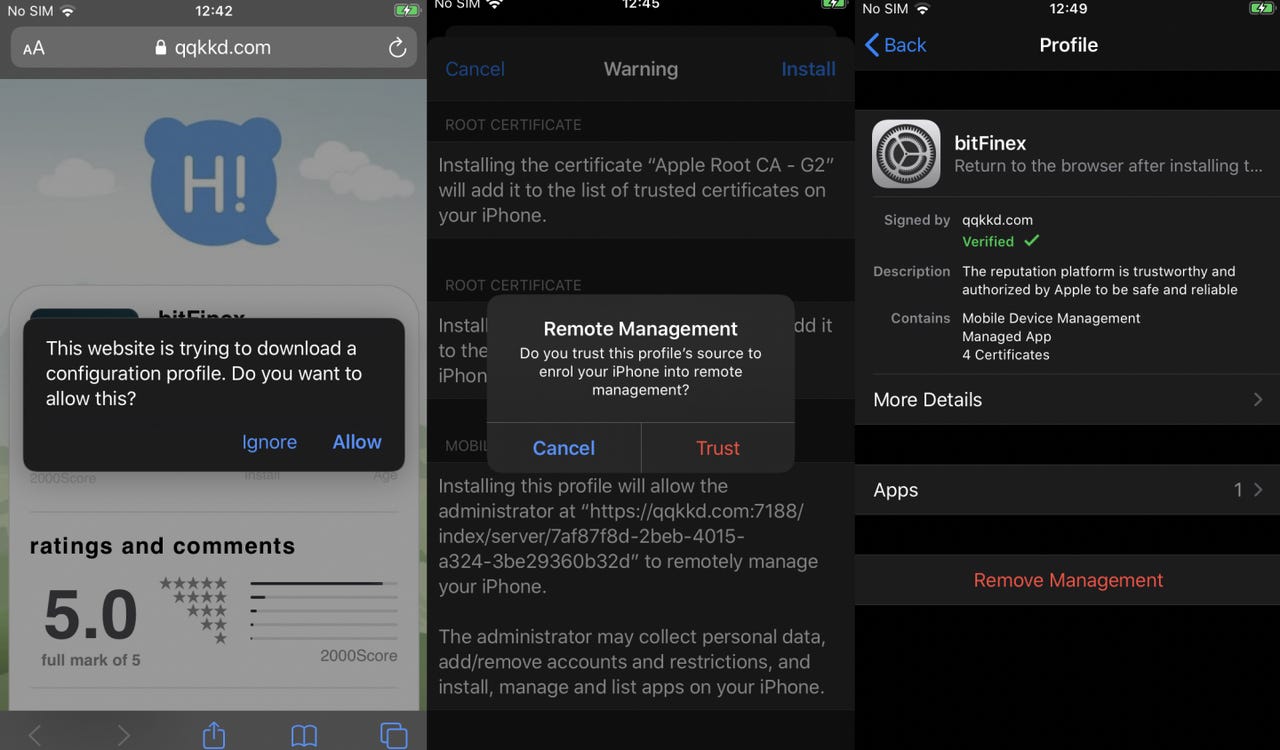
The scammers were somehow able to easily game Apple's Developer Enterprise program -- and the Apple Enterprise/Corporate Signature -- to distribute these fraudulent crypto apps, which were masquerading as Binance and other legitimate brands. Sophos said its threat hunters observed the scammers abusing Apple's Enterprise Signature to manage victims' devices remotely.
Apple did not respond to requests for comment. Sophos also contacted Apple about the issue and did not get a response.
Named "CryptoRom," according to Sophos researchers Jagadeesh Chandraiah and Xinran Wu, the scam has led to at least $1.4 million being stolen from victims in the US and EU. In their report, the two say that the attackers moved beyond going after victims in Asia and instead are now targeting people in Europe and the US.
Sophos researchers even managed to find a Bitcoin wallet that was being controlled by the attackers thanks to one victim, who shared the address he initially sent the money to before being shut out.
Chandraiah said the CryptoRom scam relies heavily on social engineering at almost every stage. Victims came to Sophos to discuss the scam and the researchers found other reports of people being taken advantage of.
"First, the attackers post convincing fake profiles on legitimate dating sites. Once they've made contact with a target, the attackers suggest continuing the conversation on a messaging platform," Chandraiah said.
"They then try to persuade the target to install and invest in a fake cryptocurrency trading app. At first, the returns look very good but if the victim asks for their money back or tries to access the funds, they are refused and the money is lost. Our research shows that the attackers are making millions of dollars with this scam."
Victims are initially contacted on apps like Bumble, Tinder, Facebook dating and Grindr before the conversation is moved to other messaging apps. From there, the conversation is steered toward getting victims to install fake trading applications onto their devices. Once a victim is drawn in, they are asked to invest a small amount before being locked out of accounts if they demand their money back.
The attack is two-pronged, giving cybercriminals the ability to steal money from victims and gian access to their iPhones. According to Wu and Chandraiah, the attackers are able to use "Enterprise Signature" -- a system built for software developers that assists enterprises with pre-test new iOS applications with selected iPhone users before they submit them to the official Apple App Store for review and approval.
"With the functionality of the Enterprise Signature system, attackers can target larger groups of iPhone users with their fake crypto-trading apps and gain remote management control over their devices. This means the attackers could potentially do more than just steal cryptocurrency investments from victims. They could also, for instance, collect personal data, add and remove accounts, and install and manage apps for other malicious purposes," the researchers said.
Chandraiah added that until recently, criminal operators mainly distributed the fake crypto apps through fake websites that resemble a trusted bank or the Apple App Store.
"The addition of the iOS enterprise developer system introduces further risk for victims because they could be handing the attackers the rights to their device and the ability to steal their personal data," Chandraiah said.
"To avoid falling victim to these types of scams, iPhone users should only install apps from Apple's App Store. The golden rule is that if something seems risky or too good to be true – such as someone you barely know telling you about some 'great' online investment scheme that will deliver a big profit – then sadly, it probably is."
Sophos published another report on a similar scam in May that was aimed solely at people in Asia. But over the last few months the researchers saw a startling expansion of the attacks.
"This scam campaign remains active, and new victims are falling for it every day, with little or any prospect of getting back their lost funds. In order to mitigate the risk of these scams targeting less sophisticated users of iOS devices, Apple should warn users installing apps through ad hoc distribution or through enterprise provisioning systems that those applications have not been reviewed by Apple," the two researchers wrote.
"And while institutions dealing with cryptocurrency have started implementing 'know your customer' rules, the lack of wider regulation of cryptocurrency will continue to draw criminal enterprises to these sorts of schemes, and make it extremely difficult for victims of fraud to get their money back. These scams can have have a devastating effect on the lives of their victims."