Spammers break Microsoft Live Hotmail CAPTCHA...again

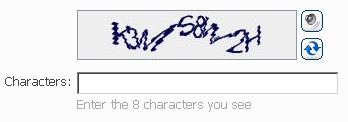
The latest version of Microsoft Live Hotmail's CAPTCHA authentication system has been broken, reports InfoWorld via security company Websense.
According to a detailed analysis of the latest hack by Websense, spammers have come up with a new scheme to fool the CAPTCHA:
The process starts in the same way as did previous CAPTCHA-breaking attacks, using bot-controlled zombie PCs under remote control to fill in the main fields - name, password, country - asked for by Hotmail during signup. The CAPTCHA image presented by Hotmail is then uploaded to a remote server for image decoding, before being sent back to the client for the attempt to create the fake account to proceed.
The latest hack comes just months after Microsoft modified the CAPTCHA to beat similar attacks, having suffered several in 2008.
Websense's analysis of the hack suggests that this process will be successful in one out of every five to 8 attempts, or between 12 and 20 percent of the time -- more than enough to offer spammers a healthy return for their efforts.
The CAPTCHA image analysis itself is said to take only 20 to 25 seconds per attempt per machine.
With its CAPTCHA under siege, Microsoft risks spammers creating large numbers of fake accounts to use as spam relays under the wings of Hotmail's trusted domain name.
The latest attack featured communication between the zombie PC and the remote host using an encrypted channel, which makes detection of such traffic more difficult.
For now, CAPTCHA remains a cat-and-mouse game: Microsoft alters its algorithm, then the spammers do.
"As we've seen from previous patterns, spammers just attack whatever system is in place. They are financially motivated to get hold of details, and will increase the sophistication of attacks, in a persistent cycle," said Carl Leonard, Websense's European threat research manager.
Making matters worse is the rapid spread of automated tools for breaking CAPTCHA on several service providers, including Google and Yahoo.