Snooping on wired keyboards overhyped

The story that wired keyboards could be snooped on caused a fair bit of brouhaha on the blogosphere.
Here's the background by researchers Martin Vuagnoux and Sylvain Pasini:
To determine if wired keyboards generate compromising emanations, we measured the electromagnetic radiations emitted when keys are pressed. To analyze compromising radiations, we generally use a receiver tuned on a specific frequency. However, this method may not be optimal: the signal does not contain the maximal entropy since a significant amount of information is lost.
Our approach was to acquire the signal directly from the antenna and to work on the whole captured electromagnetic spectrum.
We found 4 different ways (including the Kuhn attack) to fully or partially recover keystrokes from wired keyboards at a distance up to 20 meters, even through walls. We tested 11 different wired keyboard models bought between 2001 and 2008 (PS/2, USB and laptop). They are all vulnerable to at least one of our 4 attacks.
We conclude that wired computer keyboards sold in the stores generate compromising emanations (mainly because of the cost pressures in the design). Hence they are not safe to transmit sensitive information. No doubt that our attacks can be significantly improved, since we used relatively unexpensive equipments.
So, should we be pulling on our tinfoil hats and disconnecting out keyboards? Should we be running to the hills?
Not so fast there ...
I've watched the two videos posted on these attacks and a few things struck me:
- First, this experiment was conducted in a lab with the antenna seemingly close to the keyboard and the the cable between the keyboard and PC carefully straightened out. This all seems very ideal to me.
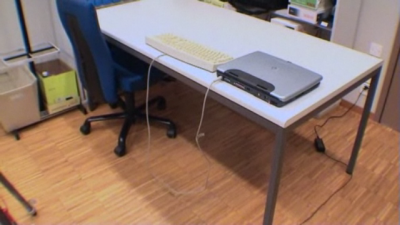
- To me it seemed that the researchers did a lot to eliminate EM noise by using only a notebook. I'd like to see this done in an environment that's EM noisy.
- Anyone else wonder why the keystroke decoding software exits as soon as "trust no one" has been typed? Shouldn't it still be waiting for more keystrokes?
I'm not worried? Is anyone else?