Skype posts "URI arguments" security alert, fix

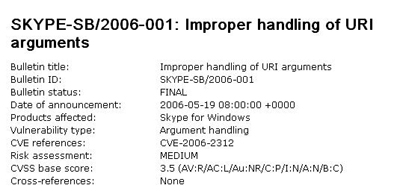
Skype has just posted a security alert entitled SB/2006-001: Improper handling of URI (Uniform Resource Identifier) arguments. There's a fix already available.
According to the alert:
An attacker who constructs a Skype URL that is malformed in aspecific way can initiate the transfer of a single named file from one Skype user to another, provided that the sender follows the malicious link and that the recipient has previously authorized the sender.
Skype notes that:
This behavior is due to incorrect parsing of the parameters passed by the URI handler. The vulnerability depends on several factors,including host configuration and the authorization relationship of the sender and the receiver.The vulnerability isn't easily triggered, but sounds like one that if an attacker would know how to trigger it, wouldn't be that difficult to pull off.
The Alert continues to note:
The attack requires the targeted user to manually follow a specially crafted malformed link, such as on a web page. Depending on several factors, doing so may result in the initiation of a file transfer, which will be accompanied by the normal Skype file transfer dialogue box. If a file transfer is started, it will be visible to the user and may be cancelled by the sender by selecting "Cancel" in the normal way.
Here's where to download the fixes:
x86 platform, Microsoft Windows 2000 or Microsoft Windows XP:
http://www.skype.com/products/skype/windows/x86 platform, Linux:
http://www.skype.com/products/skype/linux/PPC platform, Mac OS X v10.3 (Panther) or later:
http://www.skype.com/products/skype/macosx/Pocket PC platform, Microsoft Windows Mobile 2003:
http://www.skype.com/products/skype/pocketpc/