Windows 10 security: Microsoft offers free trial of latest Defender ATP features

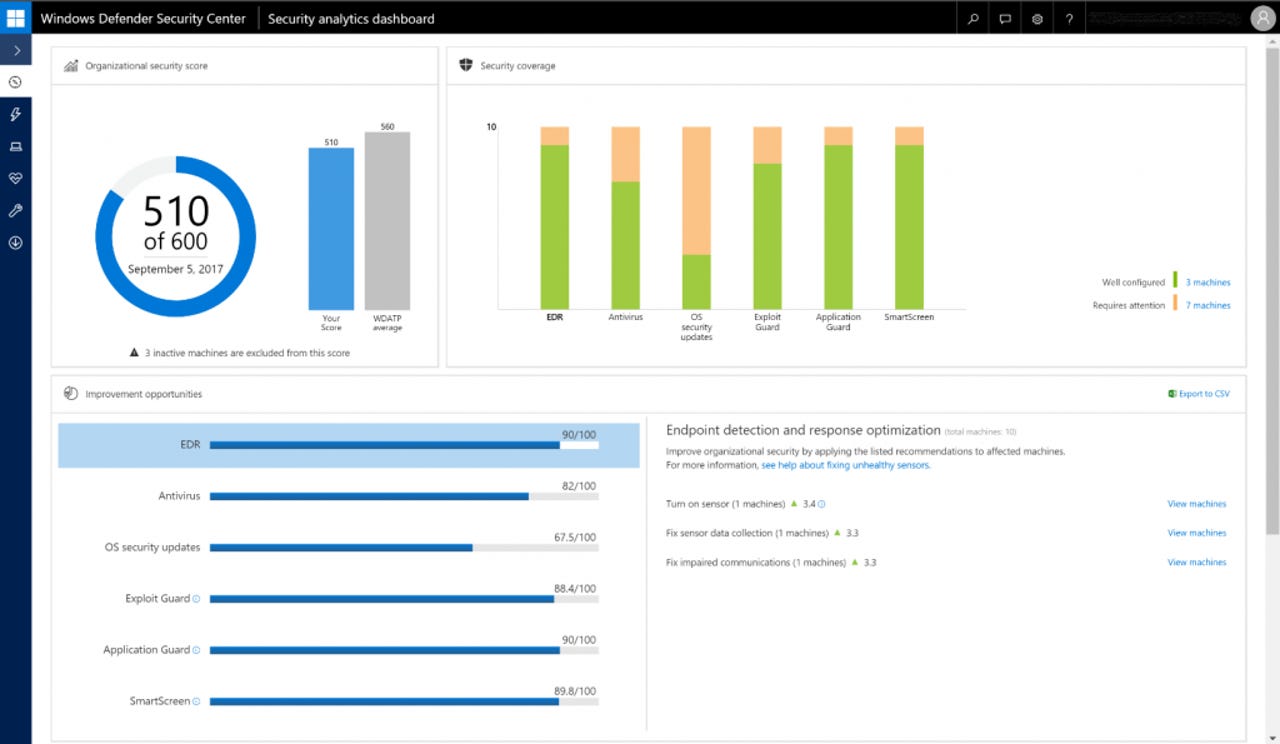
Defender ATP now comes with a new security analytics dashboard to assess an organization's overall security against Microsoft's recommended baseline.
In the wake of recent global ransomware outbreaks such as WannaCry and Petya, Microsoft has been prepping better tools to help IT security operations or SecOps detect and contain malware that makes it past defenses.
Defender Advanced Threat Protection (ATP) is the set of tools Microsoft offers to enterprise customers to detect advanced threats, as well as clean up and contain malware after a breach has occurred.
It's a Windows 10 Enterprise feature built for a world where it's assumed you'll be breached at some point. The latest version covers prevention, detection, investigation, response and management.
Customers can now adjust settings to preview the latest features Microsoft has bundled in the service. Users need to toggle on the Preview experience under Preferences setup in the navigation pane. The Fall Creators Update version of Defender ATP is available as a free three-month trial.
The updates to Defender ATP make up the bulk of Microsoft's security updates in the Windows 10 Fall Creators Update, which is expected to be available this month.
As ZDNet has reported earlier, the update introduces Windows Defender Application Guard (WDAG), which uses hardware-based isolation to protect data and system services, even if Windows or the kernel is compromised.
WDAG allows admins to define trusted and untrusted sites. Edge will open in an isolated container in the case of untrusted sites, preventing an attacker from nabbing the user's credentials.
It also features Windows Defender Exploit Guard -- formerly called Enhanced Mitigation Experience Toolkit -- integration with Intune and System Center Configuration Manager, Windows Device Guard, and improved security analytics.
Microsoft today outlined how Defender ATP will improve SecOps' visibility into key events across the organization.
Firms will now be able to see security alerts in each machine's timeline coming from Endpoint Detection and Response (EDR), Windows Defender Antivirus (AV), Windows Defender Firewall, Windows Defender SmartScreen, Windows Defender Device Guard and Windows Defender Exploit Guard.
SmartScreen will show, for example, whether an employee has clicked a link despite seeing a warning message. Device Guard will flag attempts to run any unauthorized applications.
Admins will also be able to see applications blocked by Windows Defender Exploit Guard's protection rules, as well as detections from Windows Defender antivirus and firewall.
Alerts for Device Guard and Application Guard are viewable from the Windows Defender Security Center. The console shows details about events and alerts occurring in Application Guard isolated containers.
Microsoft says it has improved how Defender ATP displays alerts to give SecOps better contextual information behind attacks, such as keylogging, network exploration, and malicious scripts. The service now automatically correlates and groups alerts for these attacks.
To help SecOps respond quickly to detected attacks, admins can now also use group machines and tagging to improve protection for high-value assets. They can also download investigation packages from machines to view their current state and study the tools and techniques used by an attacker.
Microsoft has also provided more gradual machine isolation, the ability to setup a whitelist of trusted binaries on a machine, and remotely initiate a Windows Defender antivirus scan, even if the machine is running a third-party antivirus.
Defender ATP now comes with a new security analytics dashboard to assess the organization's overall security compared with Microsoft's recommended baseline, and a new feature to create custom reports in Power BI to help analyze machines, alerts and investigation status.
Finally, Defender ATP has been expanded to cover not just desktop, but Windows Server 2012R2 and Windows Server 2016, as well as support for virtualized desktops.
Previous and related coverage
What to expect from the Windows 10 Fall Creators Update
The fourth feature update to Windows 10 is scheduled to arrive in October. It's packed with a wide assortment of new and refined features, including some new security options designed to block zero-day exploits and ransomware.
Windows 10 security: After Kaspersky fight, Microsoft talks up its case for Defender
Windows 7 machines mostly unprotected because they're not running any antivirus, says Microsoft.
More on security
- Security firm Mandiant said to be helping Equifax in hack aftermath
- Credit rating giant Equifax admits hack; as many as 143 million affected
- Alexa, Cortana, Google, Siri user? Watch out for these inaudible command attacks
- Locky ransomware: Why this menace keeps coming back
- Android security: Google patches dozens of dangerous bugs, including some in Oreo