Shade (Troldesh) ransomware shuts down and releases decryption keys

The operators of the Shade (Troldesh) ransomware have shut down over the weekend and, as a sign of goodwill, have released more than 750,000 decryption keys that past victims can now use to decrypt their files.
Security researchers from Kaspersky Lab have confirmed the validity of the leaked keys and have released a free decryption tool.
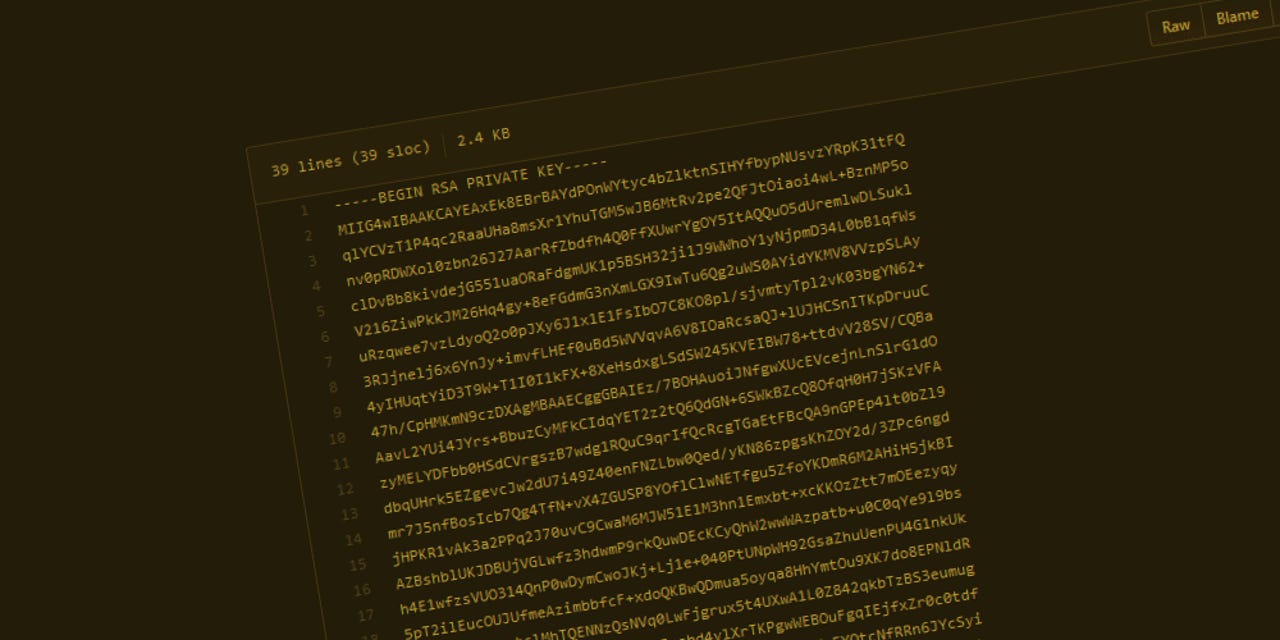
In a short message posted in a GitHub repository, the Shade team explained what led to their decision.
We are the team which created a trojan-encryptor mostly known as Shade, Troldesh or Encoder.858. In fact, we stopped its distribution in the end of 2019. Now we made a decision to put the last point in this story and to publish all the decryption keys we have (over 750 thousands at all). We are also publishing our decryption soft; we also hope that, having the keys, antivirus companies will issue their own more user-friendly decryption tools. All other data related to our activity (including the source codes of the trojan) was irrevocably destroyed. We apologize to all the victims of the trojan and hope that the keys we published will help them to recover their data.
While the Shade gang explained why they released the decryption keys, they did not explain why they shut down. Several theories have started to form among ransomware experts, yet none are based on actual tangible threat intelligence.
Prior to shutting down at the end of 2019, the Shade ransomware has been one of the oldest ransomware strains, being first spotted in 2014 and operating almost non-stop until it shut down last year.
It was also one of the most most active ransomware operations [1, 2], being distributed via a combination of email spam campaigns and exploit kits.
The ransomware wasn't perfect, though, and during its lifetime, security researchers from Kaspersky and Intel Security (now McAfee) have released multiple decryption apps that could help victims recover files. However, the decrypters only worked against a small number of Shade versions, and the last of these tools was released in 2017.
The decryption keys released today will help all users who had files encrypted by the Shade ransomware. The keys are believed to account for all versions of the ransomware and all users who ever got infected.
The only condition is that users still have the encrypted files laying around, so they can be decrypted.
While security experts often recommend saving ransomware-encrypted files on an offline hard drive, most victims simply reinstall their computer from scratch, deleting the encrypted data. Those who saved their encrypted files can now recover data they once considered lost.
Updated on May 1 with a link to Kaspersky's free decryption tool.