Second WordPress hacking campaign underway, this one targeting AMP for WP plugin

A second vulnerability in a high-profile WordPress plugin has come under active exploitation in the span of a week, ZDNet has learned from WordPress security firm Defiant.
Security
Attacks are currently ongoing, the company said today in a detailed blog post after ZDNet reached out for comment yesterday. This is the second separate wave of hacking attempts detected against WordPress sites after Defiant discovered last week a similar hacking campaign aimed at WordPress sites using the WP GDPR Compliance plugin.
But for this most recent hacking campaign, hackers are targeting a vulnerability that impacts AMP for WP (formerly Accelerated Mobile Pages), a WordPress plugin installed on more than 100,000 sites.
This vulnerability came to the general public's attention last week after web security firm WebARX published proof-of-concept code on how to exploit it on its blog.
ZDNet: Black Friday 2018 deals: Business Bargain Hunter's top picks | Cyber Monday 2018 deals: Business Bargain Hunter's top picks
However, the actual vulnerability was discovered by a Dutch security researcher named Sybre Waaijer, who found and reported the issue to the maintainers of the WordPress Plugins repository in mid-October.
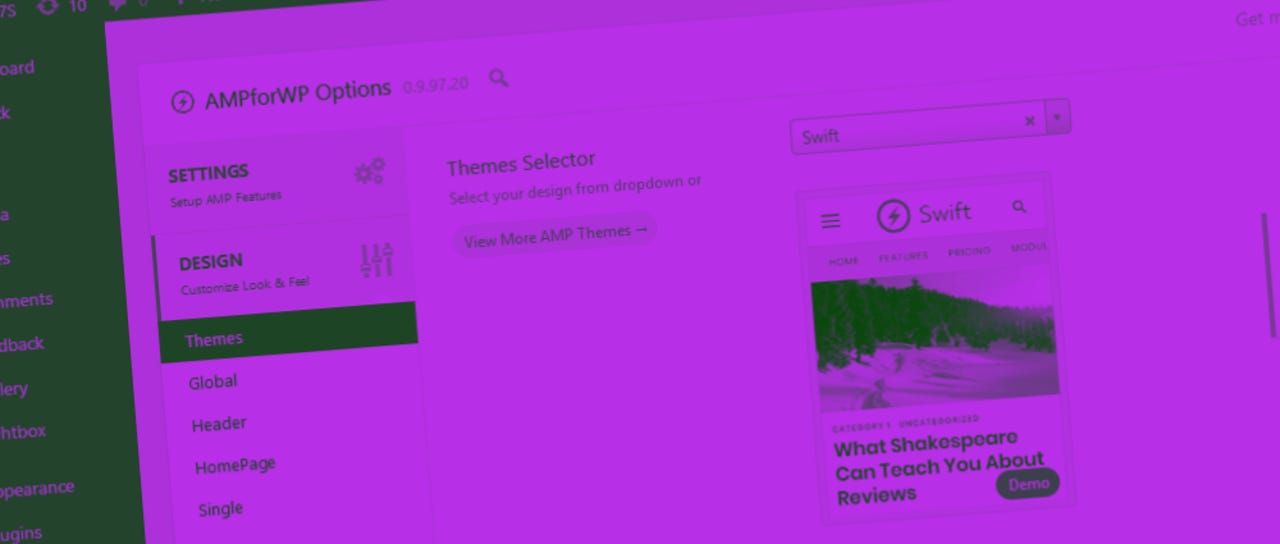
The AMP for WP plugin was removed from the official WordPress Plugins repo between October 22 and 31, as developers worked and released a security fix for the reported issue (AMP for WP version 0.9.97.20).
The vulnerability is similar to the one reported in the WP GDPR Compliance plugin, as attackers can use the plugin's vulnerable code to make site-wide changes to site options to which the plugin shouldn't have had access to.
But it appears that the publication of the proof-of-concept code last week had drawn hackers' attention to this largely unknown issue. Now, Defiant experts say, that hackers have incorporated this new vulnerability into a "sophisticated attack campaign."
The campaign is warranted of the "sophisticated" tag because hackers aren't just blindly abusing the AMP for WP vulnerability directly, but have combined it with another cross-site scripting (XSS) security bug.
Attackers scan the web for vulnerable sites using the AMP for WP plugin, use the XSS vulnerability to store malicious code in various parts of the sites, and wait for an admin user to access those site sections.
The malicious code loads a JavaScript file from the sslapis.com domain which attempts to call URLs only accessible to users with admin accounts.
According to Defiant, this JavaScript code will allow hackers to create an admin user named "supportuuser", but will also access the code editor section of other plugins, where they plant other malicious code that acts as a backdoor in case the "supportuuser" account is removed.
The campaign is in full force, Defiant warns, and WordPress site admins should update the AMP for WP plugin as soon as possible, and review if a new admin user account named "supportuuser" has appeared out of the blue in their site's backend.
WordPress 5.0 is out. Here's a tour of the new features!
More security news:
- Hackers use Drupalgeddon 2 and Dirty COW exploits to take over web servers
- Card skimming malware removed from Infowars online store
- Popular Dark Web hosting provider got hacked, 6,500 sites down
- One in five Magecart-infected stores get reinfected within days
- Access data for 70% of top US & EU websites sold on the dark web TechRepublic
- Website geoblocking is not that widespread, study finds
- Researchers find stolen military drone secrets for sale on the dark web CNET
- A bug in EA Origin client exposes gamers' data
Best Black Friday 2018 deals:
- Amazon Seven Days of Black Friday Deals: All-time lows on office devices
- Amazon Black Friday 2018 deals: See early sales on Echo, Fire HD
- Best Buy Black Friday 2018 deals: Deep discounts on Apple Mac, Microsoft Surface
- Target Black Friday 2018 deals: $250 iPad mini 4, $120 Chromebook
- Walmart Black Friday 2018 deals: $99 Chromebook, $89 Windows 2-in-1
- Dell Black Friday 2018 deals: $120 Inspiron laptop, $500 gaming desktop
- Newegg Black Friday 2018 deals: $50 off Moto G6, $70 off Nest thermostat
- Office Depot Black Friday 2018 deals: $300 off Lenovo Flex, $129 HP Chromebook
- eBay Black Friday 2018 deals: See early sales on Galaxy Watch, Chromecast
- Lenovo Black Friday 2018 deals: ThinkPad laptops and more
- Microsoft Store Black Friday 2018 deals: Ad showcases Surface, laptop deals
- Windows laptops Black Friday deals: Dell, HP, Lenovo
- Chromebook Black Friday 2018 deals: Dell, Google, HP
- Best tablet Black Friday deals: Apple iPad, Amazon Fire
- Black Friday 2018 iPhone deals: $400 iPhone X gift card, BOGO iPhone XR
- Black Friday 2018 smartphone deals: OnePlus 6T, LG G7